Operations | Monitoring | ITSM | DevOps | Cloud
StatusCast Top Picks: 10 More Awesome Customer IT Status Pages
IT services are a critical backbone to the operations and functioning of most every business and organization. As more and more IT departments have embraced the need for good governance, this has driven greater transparency. From the perspective of IT service management, this has manifested itself as much greater openness when communicating about IT service availability.
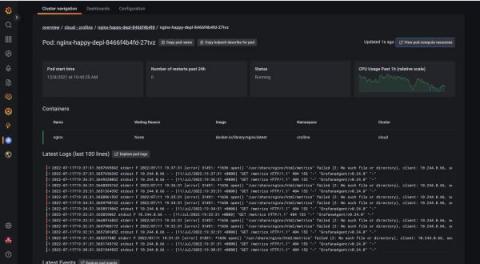
Introducing instant Kubernetes logging with Kubernetes Monitoring in Grafana Cloud
Kubernetes, Prometheus, and Grafana are a trio of technologies that have transformed cloud native development. However, despite how powerful these three technologies are, developers still face gaps in the process of implementing a mature Kubernetes environment.
Amazon Drive or Amazon Cloud Drive: Which One Is It? And Is Amazon's Cloud Service Any Good?
Driving Innovation Aligned with the AWS Security Competency Re-launch
Logz.io recently obtained the Amazon Web Services (AWS) Security Competency for our Cloud SIEM. We are thrilled to support the re-launch of the AWS Security Competency, as clearly the only way to combat today’s cybersecurity challenges is to modernize your analytics platform to respond to today’s evolving threat landscape.
How to use GitHub Actions securely
GitHub is one of the most popular source control platforms available. It relies on Git concepts, and millions of developers use it. GitHub Actions embrace all aspects of what source control needs, such as branching, pull requests, feature flags, and versioning. It also integrates nicely into third-party continuous integration and continuous development (CI/CD) pipelines or deployment tools like Azure DevOps, Jenkins, GitLab, and Octopus Deploy.
An example of a hyperautomation journey
Nick Borgwardt, director of IT workflow at ServiceNow, co-authored this blog. In our personal lives, it’s easy to get the information and products we need with just a few clicks. Thanks to modern consumer websites and apps, making service requests and ordering products is simple, convenient and, often, automatic. Why shouldn’t our professional lives be just as effortless?
SIP Trunk with Teams Phone Explained
SIP trunking is a great way to improve your business’s communication system. It is cost effective and scalable, and it offers many features that traditional systems do not. In this article, we’ll give you a quick introduction to SIP trunking, how it can benefit your business and how to easily monitor it when linked to Microsoft Teams.
The Service Value Chain in ITIL 4
How to Manage Your Data Center During a Heatwave
The recent heatwave that brought record temperatures to the UK caused cooling systems to fail at a London data center resulting in downtime for Google and Oracle. According to Oracle, “Following unseasonably high temperatures in the UK south (London) region, two cooler units in the data centre experienced a failure when they were required to operate above their design limits.