Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on CyberSecurity for Applications, Services and Infrastructure, and related technologies.
7 Reasons To Choose SafeOpt Over Other Online Retail Software Options
Introducing the Cribl Pack for Corelight
In this blog series, we’ll explore how Corelight and Cribl Stream work together to improve observability in Security Operations Centers (SOCs). In today’s rapidly changing threat landscape, it’s crucial to efficiently monitor and manage data for effective security operations. Corelight provides exceptional network visibility, while Cribl Stream gives you control and the flexibility to optimize data pipelines and gain valuable insights.
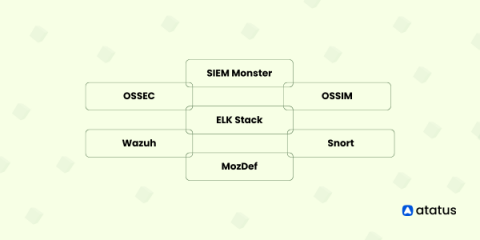
Top Open Source SIEM Tools
In the fast-paced world of cyber security, organizations face a challenging task to safeguard their digital assets from a variety of advanced threats. Security Information and Event Management (SIEM) tools have emerged as a vital solution, empowering businesses to detect, respond to, and mitigate security incidents effectively.
9 Foolproof Ways to Protect Your Employee Privacy
Cybercrime is one of the greatest threats to modern businesses, so naturally, cybersecurity is becoming a top priority among business leaders worldwide. It’s easy to see why. Cybercrime can result in significant losses for companies, particularly financially. In fact, the global cost of cybercrime is expected to rise to $23.84 trillion by 2027, up from $8.44 trillion in 2022. Businesses collect and store mountains of data daily, and are obligated to keep that data secure.
The key to secure transmission: TLS in the Raygun ecosystem
HAProxy and Let's Encrypt: Improved Support in acme.sh
TLS certificates are crucial for the secure flow of web traffic, but managing these digital certificates can pose a challenge. Using an ACME-based certificate authority like Let’s Encrypt can automate and simplify the management of issuing these certificates. Certificate management in HAProxy has steadily improved over the years, allowing it to become more flexible and load certificates without restarting.
How Kentik Helps You Mitigate Cyberattacks Faster
No matter how much prevention you have, serious security incidents will inevitably occur. Read the next article in our security series that covers how to understand cyberattacks as quickly as possible so that your organization can respond swiftly.
Why Cyber Resilience Is Foundational to Your SIEM Success
The common failure scenarios that occur in the cybersecurity world are typically assumed to be costs of doing business, but they’re actually more predictable and avoidable than you might imagine. Even if you’ve been lucky enough to avoid failed data sources or backups, a SIEM getting knocked offline, and other cybersecurity attack situations until now — in today’s day and age, they’re still inevitable.
IT in Motion Podcast: Protecting your Data from the Dark Side
Longtime ScienceLogician Tim May joins the podcast for an entertaining discussion surrounding the number of different roles he's held within the organization in his 17 years with ScienceLogic, and a glimpse into his admiration of Star Wars! https://sciencelogic.com/product/resources/protecting-your-data-from-the-dark-side