Time Series Forecasting Use Cases and Anomaly Detection
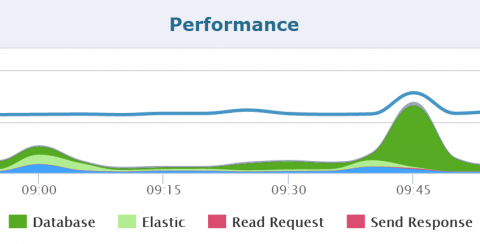
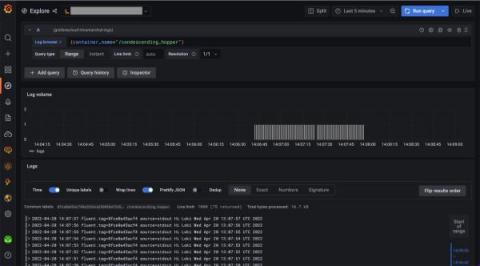
Wouldn’t it be great to peek into the future and find answers to the problems that you’re facing today? This may sound like science fiction, but many companies currently possess this capability, and they are creating strategies around it to strengthen their monitoring and analytical capabilities. One way is time series forecasting, a statistical method. You can take advantage of the insights of time series forecasting by using techniques like anomaly detection to gain.