Operations | Monitoring | ITSM | DevOps | Cloud
10 Ideal Appointment Scheduling Tools
Companies need special scheduling tools to organize and plan events, tasks, and various facilities. The business executives and managers or various projects need to be well-versed in their upcoming course of action. They need to plan their week accordingly, to decide when to attend meetings, events, and when to attend to clients. By planning their whole day, they will have time to make payments and perform their respective roles and responsibilities without any hassle.
Data Security Management and Control 101: What Is Data Loss Prevention?
Companies and businesses of all sizes collect and save all types of data. This data can be valuable to others if it were to be leaked outside the business. Data security management and control using the right data loss prevention (DLP) solutions are necessary to protect this and other types of data. So, what exactly is DLP? In general, DLP consists of the tools, apps, and other data loss prevention techniques businesses implement to keep their data safe and secure.
The Importance of Communicating Scheduled Maintenance to End-Users
Often, outages are planned. In fact, in most organizations, outages are typically not caused by something going wrong, but because some kind of IT operation requires your team to take a system temporarily offline. Communicating scheduled maintenance is just as important, if not more important than alerting users to unplanned outages.
The New Normal: Organizations Need Security Leaders More Than Ever
The world is changing at a pace not seen in modern history. Security leaders, including chief information security officers (CISOs), face new security challenges as well as opportunities. As COVID-19 drives workers to look for new ways to live and work, organizations must be proactive. The ‘new normal’ may seem scary at first, but savvy CISOs who see beyond tactical changes to the threat landscape can capitalize on opportunities.
Security operations center, Part 1: The guardian of your organization
Hackers arm themselves with the latest technologies, employ different techniques, and try to exploit all possible vulnerabilities in the security of an organization. With these tools under their belt, hackers will persist until they get what they want. To stay one step ahead of hackers and remain up to date on cutting-edge technologies, your organization needs a dedicated team whose main objective is to detect and stop cyberattacks that threaten it.
Best practices for maintaining end-to-end tests
In Part 1, we looked at some best practices for getting started with creating effective test suites for critical application workflows. In this post, we’ll walk through best practices for making test suites easier to maintain over time, including: We’ll also show how Datadog can help you easily adhere to these best practices to keep test suites maintainable while ensuring a smooth troubleshooting experience for your team.
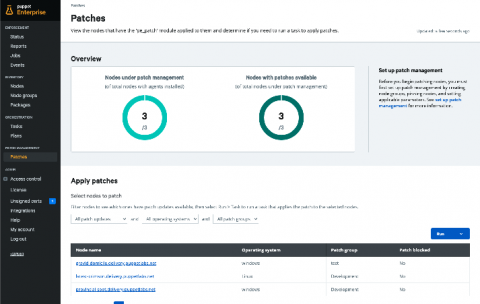
Standardize and automate patching workflows with Puppet Enterprise
Patching systems is not a new problem; this is something that organizations are very familiar with. Organizations have tried solving this issue in various ways by cobbling together multiple tools, processes, different teams, and more. Organizations are constantly trying to stay secure and keep their systems up to date, but patch management isn’t a simple process. In fact, applying the patch itself is just one part of the overall workflow, which involves multiple teams and various steps.
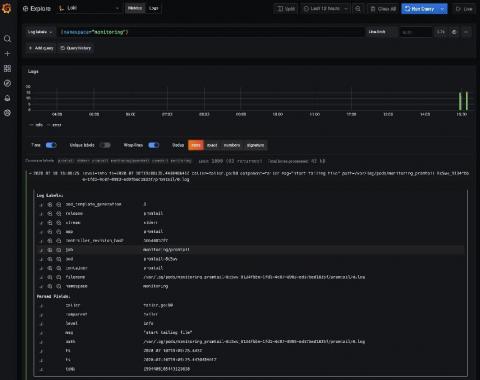
Loki tutorial: How to send logs from EKS with Promtail to get full visibility in Grafana
Amazon Elastic Kubernetes Service (Amazon EKS) is the fully managed Kubernetes service on AWS. If you’re using it and wondering how to query all your logs in one place, Loki is the answer. With this tutorial, you’ll learn how to set up Promtail on EKS to get full visibility into your cluster logs while using Grafana. We’ll start by forwarding pods logs then nodes services and finally Kubernetes events.
12 Container image scanning best practices to adopt in production
Don’t miss out on these 12 image scanning best practices, whether you are starting to run containers and Kubernetes in production, or want to embed more security into your current DevOps workflow. One of the main challenges your teams face is how to manage security risk without slowing down application delivery. A way to address this early is by adopting a Secure DevOps workflow.