Operations | Monitoring | ITSM | DevOps | Cloud
Monitoring and Managing Azure Active Directory Users
This blog post is part 2 of our Monitoring Microsoft Azure Active Directory series. Managing Identity is a big challenge in a cloud environment, especially when users can potentially log in from anywhere. Additionally, users can often use different types of devices to log in and access cloud-hosted resources. Without a central Authentication and Authorization source, it is very difficult to manage who can login to what and who can do what with a cloud resource.
Azure Active Directory (Azure AD) - 101
This is a multi-part series that covers monitoring Microsoft Azure Active Directory (AD). In this blog post, which is part 1 of the series, you will learn about and understand Microsoft Azure Active Directory (Azure AD) and how it is different from an on-premises Active Directory (AD). As technology keeps evolving, companies increasingly look to technologies like Cloud Computing to expand, modernize and stay competitive, and in doing so companies can expose themselves to risks.
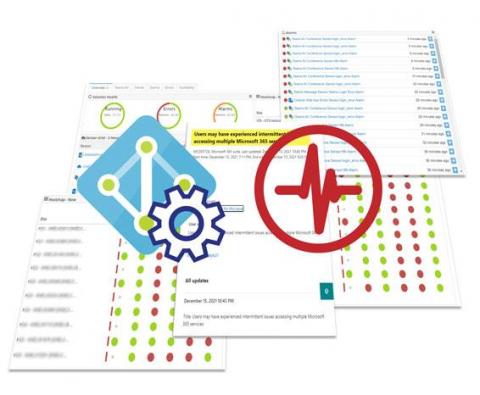
Global Azure AD Outage Affecting Microsoft 365 Services December 15
Microsoft has had its own share of outages recently and during the evening of December 15th Azure AD was the cloud culprit. As a result, the Exoprise sensors detected this Microsoft 365 outage more than an hour before Microsoft informed customers of the issue. Here’s some of the errors that users were experiencing if they attempted to sign into Microsoft services: Most of our worldwide customers knew well in advance of the problem before users or business suffered.
What causes repeated account lockouts and how to resolve them
A stringent account lockout policy is vital to derail password guessing and brute-force attacks but it also runs the risk of locking out legitimate users costing businesses valuable time, money, and effort. With password reset requests accounting for almost 30% of the total IT help desk tickets, resolving frequent account lockouts becomes an indispensable part of a sysadmin’s job.
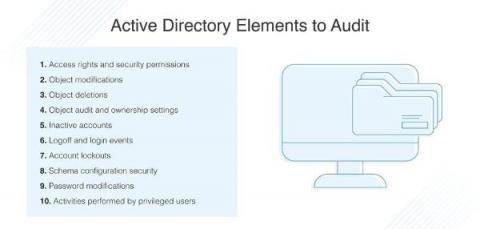
Investigation of AD Security Breaches
Active Directory DL Teams
How to Monitor Microsoft Azure Active Directory (Azure AD)
Do you already know what Active Directory is and how to use it with Pandora FMS?
As you may already know, in this blog, we’re so into answering the big questions. After answering in previous episodes what the meaning of our existence is or explaining everything you need to know about Office 365 Monitoring, in today’s episode we are going to discuss what Active Directory is. I hope you are very comfortable sitting in your respective gamer chairs or in your two-seater sofas, because here we go!