Operations | Monitoring | ITSM | DevOps | Cloud
Why Use Active Directory Security to Improve Your Server Security?
How do you secure your network servers, laptops, desktops, and workstations? A good starting point is to have a checklist of how to enable security features on these devices. You also need to enable a server monitoring service to track specific events and generate event logs. Yet, your security tasks are never done. You can get a false sense of security if you merely go through your checklist of security items and stop.
Active Directory Security Best Practices Includes Monitoring for Signs of Compromise
Fun Fact: Most types of network and computer compromises could have been discovered much sooner if the organization had enabled proper event log monitoring using an appropriate server monitoring solution that alerted them to the issue. Without such a software application or not taking the time to configure it correctly, it takes much longer to uncover the compromise if it is ever discovered at all.
How Active Directory Management Tools Help Quickly Find and Troubleshoot Issues
Active Directory is part of Microsoft Windows software environments primarily for networks where some sort of domain control is required. The service is much more than just authenticating and authoring access to network resources. Active Directory is also used to enforce various network security policies, enable various processes, and enable various services. Active Directory consists of a logical structure that allows the server to execute the appropriate actions, authentication, services, and so on.
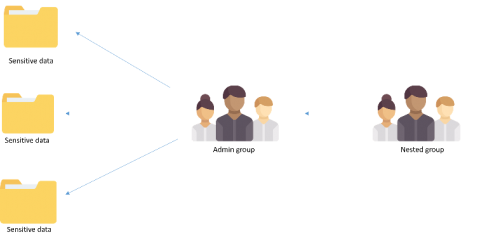
IT security under attack: Why are group memberships so crucial?
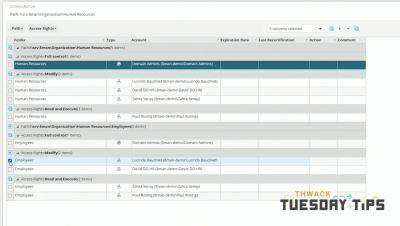
Security groups either make or break your IT security. Group memberships are responsible for administrative access in your your network and define access to other privileged resources and data on your domain. Ever wondered how a simple misconfiguration of a group membership could lead to a security incident? This blog elaborates the most common misconfiguration or security loopholes that can cause damage to the sensitive data in your network.
The importance of Active Directory for Fast Citrix Logon Time
Most of you know that one of the most important user experience metrics in a Citrix environment is the logon time. A 2018 survey by eG Innovations and DABCC found out that Citrix logon time was the number one problem for administrators: 59% of respondents rated logon time as their biggest problem. There are many best practices to improve Citrix logon times. Slowness during the logon processing can, of course, increase logon times. Issues with group policies or slow profile loading is often a cause.
Use Active Directory Monitoring to Protect Remote Active Directory Logins
Active Directory (AD) is a process service that is used in Microsoft® Windows-based environments. It is responsible for authenticating users when they connect to servers and for authorizing access to different directories, files, and data. AD is also responsible for carrying out security protocols on all connected devices and computers. For example, there is a policy in place where, after three login attempts, a user’s account is locked.
Secure mobile Authentication with Azure Active Directory
Enterprise Alert is the premier solution for reliable, targeted, and accountable Alerting. At Derdack, we have always aimed to provide the best possible security combined with an easy to use User interface. Part of this UI is the Enterprise Alert mobile App which supports secure 2-factor authentication by integrating with ADFS.
Active Directory Monitoring Essential Guide
An effective active directory monitoring system is essential to a secure directory design. There is a wide variety of security issues and loopholes that can be identified early if the users on the network are following the active directory monitoring guidelines. The lack of such monitoring can lead to a multitude of security threats which can result in financial and reputational damage along with data loss.
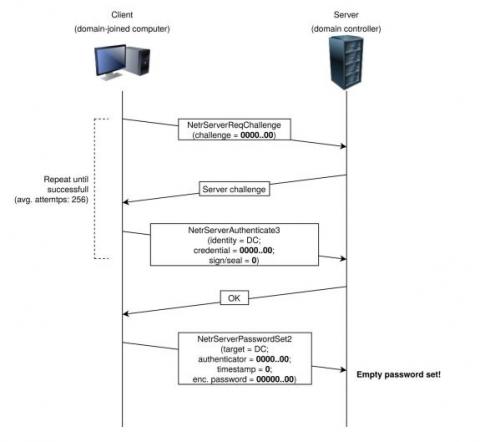
Domain controller patch alert! Vulnerability grants domain admin access in 10 seconds
A critical Active Directory vulnerability (CVE-2020-1472) has been making headlines for being the most notorious elevation of privilege bug because it can affect all computers and domain controllers in an organization. This high-risk vulnerability, dubbed Zerologon, gives threat actors easy, instant access to domain controllers without requiring any additional privileges. This attack does not even require a user to be authenticated; the user just needs to be connected to the internal network.