Operations | Monitoring | ITSM | DevOps | Cloud
What is Zero-Trust? How can it be a game-changer for the security, control, and monitoring of your IT infrastructure?
Kentik moves up the stack with Synthetic Transaction Monitoring
In our quest to provide the leading network observability solution, Kentik has been focused on developing a service for NetOps teams that empowers them to have intimate knowledge of their network traffic and the devices that route traffic. Our service helps them plan capacity, project costs, optimize routes, detect unwanted traffic, troubleshoot issues and analyze events.
11 Questions You Should Ask About Your Cloud Security
DevOps 101: Introducing Database DevOps
AppSignal's Next Level Of Front-end Error Tracking
Today we launch the next level of AppSignal front-end error tracking. We’ve made two major improvements: line-of-code-based error grouping and sourcemapped backtraces in notifications.
Scaling Engineering Teams: Perspective from our VP of Engineering
At Catchpoint, my role can be summarized at a high level as two halves: designing and taking care of Engineering teams – and working with those teams to design and take care of the various distributed systems that run our platform. I recently attended Sapphire Ventures' Hypergrowth Engineering Summit (thank you David Carter and Sapphire for the invitation!) where the sessions focused on creating and scaling high functioning engineering.
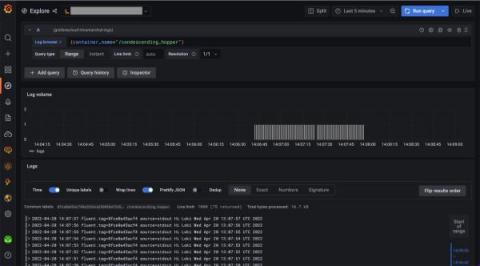
How to send logs to Grafana Loki with the OpenTelemetry Collector using Fluent Forward and Filelog receivers
In this guide, we’ll set up an OpenTelemetry Collector that collects logs and sends them to Grafana Loki running in Grafana Cloud. We will consider two examples for sending logs to Loki via OpenTelemetry Collector. The first one shows how to collect container logs with a Fluent Forward receiver. The second one shows how to collect system logs with a Filelog receiver.
7 Essential Tips For Choosing The Best Domain Name and Why it Matters
Choosing a domain name is a task that requires your full attention and should be thought about long before you undertake your website launch checklist. An inappropriate or poorly thought-through domain name is something you'll be stuck with for the foreseeable future. Domain names are tricky to change and can lead to serious SEO complications for your brand. By researching, you'll be better informed to choose a domain that works for you by maximizing website traffic and driving business revenue.
Anomaly rate in every chart
A month ago, we introduced unsupervised ML & Anomaly Detection in Netdata, the Anomaly Advisor. Today, we’re happy to announce that we’re bringing anomaly rates to every chart in Netdata Cloud. Anomaly information is no longer limited to the Anomalies tab and will be accessible to you from the Overview and Single Node View tabs as well. This will make your troubleshooting journey easier, as you will have the anomaly rates for any metric available with a single click.