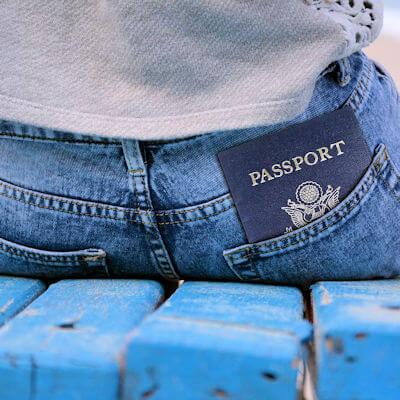
4 Tools to Help Protect Against Online Identity Theft
Online identity theft has become a significant concern for everyone, especially as we rely more on the internet for various activities such as shopping, banking, and socializing. Identity theft occurs when someone steals personal information, such as name, address, social security number, or credit card details, to commit fraudulent activities. The consequences of identity theft can be severe: $15.1 billion in monetary loss in a given year alone!