Operations | Monitoring | ITSM | DevOps | Cloud
Security
The latest News and Information on CyberSecurity for Applications, Services and Infrastructure, and related technologies.
Battle the Ransomware Scourge with Deep Network Insight
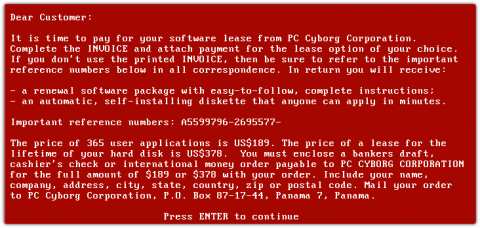
Ransomware is the gift that keeps on giving. Old as it is (33 years) ransomware is constantly morphing into new exploits. The reason is simple. Ransomware works and too often cybercriminals walk away with bags of money (or piles of Bitcoin, anyway). “Following the World Health Organization's AIDS conference in 1989, Joseph L. Popp, a Harvard-educated biologist, mailed 20,000 floppy disks to event attendees.
The Internet's Mid-Life Crisis - Black Hat at 25
“Why is it so bad right now? Why does it seem like we’re fighting this up-hill battle?” The internet, it seems, is having a mid-life crisis. As industries progress through their life cycle, they are expected to reach a quasi-steady state of maturity, but the internet hasn’t gotten that message. In fact, it seems to be stuck in the growth phase, expanding exponentially with no end in sight, and securing it just feels so hard. Let’s dive into my Black Hat recap.
How Can Startups Affordably Embrace Cybersecurity?
Red Team vs. Blue Team: The InfoSec Color Wheel
Best Practices for Navigating the Security Poverty Line
InfoSec, like any other aspect of IT, is a matter of three factors coming together: people, process and technology. All of these factors cost time and money in some way. The truth is, there are very few organizations out there who can supply their own security programs, staff, technology, processes and everything needed for InfoSec to an efficient degree. Everyone has to compromise in some way.
RESOLVE '22: The SOC and the NOC
In our RESOLVE ’22 event The SOC and the NOC, moderator and 3 Tree Tech VP of Cybersecurity Kris Taylor welcomed two esteemed guests to the stage: As Kris noted at the top of the event, we brought our panelists together to talk about “the culture of the network operating center (NOC) and security operations center (SOC).” Along the way, they discussed different philosophical and practical takes on the high-level topics of networking and security.
Troubleshooting microservices: Challenges and best practices
When people hear ‘microservices’ they often think about Kubernetes, which is a declarative container orchestrator. Because of its declarative nature, Kubernetes treats microservices as entities, which presents some challenges when it comes to troubleshooting. Let’s take a look at why troubleshooting microservices in a Kubernetes environment can be challenging, and some best practices for getting it right.
What Are Managed IT Services?
The Key Principles of Data Protection (EU, and North America)
There’s no doubt that the typical modern enterprise generates large amounts of data that must be moved, analyzed, and safely stored. Because much of this data involves the privacy of users and customers, various laws and regulations have been created to drive strong protection practices. While these regulations vary a great deal from country to country, the underlying concept remains the same: keep data safe while making it available to authorized users when they need it.