Operations | Monitoring | ITSM | DevOps | Cloud
Ivanti We Do Unify IT
Top 10 AppSignal Blog Posts in 2019
Hi there stroopwafel fans As we’re looking forward to publishing more Ruby, Elixir, and JavaScript posts in the coming 2020, we decided to take a look back at the blog posts that you gave the most hearts on Twitter, reads on the blog, and that we got the most appreciation for in 2019.
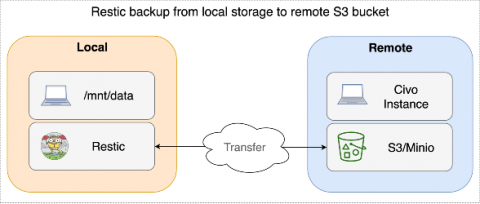
Our Top 10 Kubernetes and Cloud Native Guides For 2019
2019 has been a great year for cloud native technologies. This year we launched the world's first managed Kubernetes service back-ended by Rancher's k3s distribution, opened the #KUBE100 beta, and watched our users create some really neat things on our platform. To that end, we wanted to highlight some of our top posts from the wider Civo community, and posts that showcase the exciting state of play of the cloud native landscape at the moment.
Create your own Docker containers to test and deploy applications
If you are a developer, a systems administrator, you work in the information technology sector or you are simply a technology enthusiast who has ever deployed some type of application, surely you will have faced the same problem we all ran into. If you are thinking of dependencies, bingo!
How To Make Your Customers Happy, with Eaze
A couple of weeks ago I had the great pleasure of hosting CJ Silverio, Principal Engineer, and Ben Gardella, Manger of Infrastructure from Eaze for a clue- and cackling-filled webcast interview.
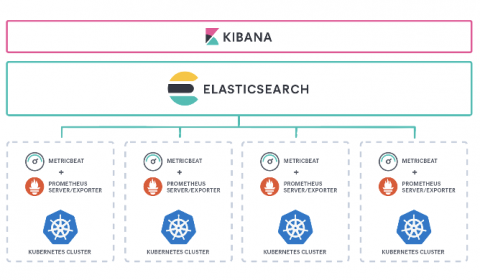
Prometheus monitoring at scale with the Elastic Stack
Tools. As engineers we all love great tools that help our teams work productively, resolve problems faster, be better. But tools can tend to grow in number, require additional maintenance, and most importantly, create silos. Each team has certain responsibilities and is constantly searching for tools that can address specific requirements in the best possible way.
Phil Tee: Observability Requires the Marriage of AI, Metrics and Logs
Observability without AIOps is just noise.
A New Framework for Hybrid Cloud Management
In recent months, the major cloud and tech players have been unfurling their latest products and strategies to win enterprise dollars. One trend that’s catching fire is hybrid infrastructure management: the need to support a mix of on-premises, private cloud, and public cloud resources.
Strengthening cybersecurity with log forensic analysis
Any system connected to the Internet is vulnerable to malicious attacks and breaches. If it’s online, there’s someone out there trying to break into it and do something bad with it (usually stealing data). Plain and simple. To protect your most valuable assets, you need bulletproof security measures, a skilled SecOps team, robust investigation tools, and reliable prevention/mitigation strategies.