Operations | Monitoring | ITSM | DevOps | Cloud
Dark Theme is here
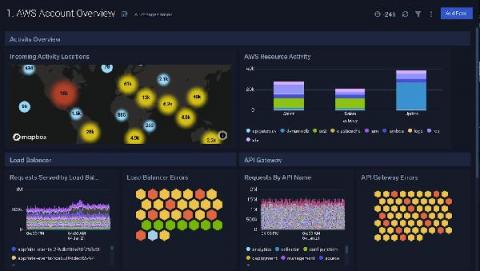
Best Data Visualization Tools for a Winning Business Presentation
Data visualization is a simple presentation of data or information in a graphical format. Humans are naturally drawn to colors and patterns and these tools make it easier for people to interpret and understand data. Numbers are complex and they can be difficult to understand conceptually. Whereas, data visualization or pictorial representation can spark an interest in your audience to listen and learn more from your presentation.
Centralized Log Management for Optimizing Cloud Costs
Centralized Log Management offers the visibility you need to optimize your cloud usage to keep infrastructure costs down. Cloud-first infrastructures are the future of modern business operations. As organizations like Google and Twitter announce long-term plans for enabling a remote workforce, maintaining a competitive business model includes scaled cloud services adoption. While the cloud offers scalability that can save money with pay-as-you-need services, managing the costs is challenging.
Better customer experiences with Raygun and Heroku
Node.js Garbage Collection: Heap Statistics Magic Dashboard
We just released a Magic Dashboard for Garbage Collection stats for our Node.js integration. If you are leaking memory, this dashboard will help you discover and fix this problem. No setting up is required, this dashboard will magically automatically appear among the rest of your dashboards. ✨
How to serve policy from a local git server
Several months ago I started the practice of using CFEngine Enterprise and its Mission Portal UI on a daily basis to manage the connected devices in my home. To start, I brought up an old desktop machine, cfengine-hub, to use as my hub and downloaded Enterprise, which is free for use up to 25 hosts. The next step in using best practices is to deploy policy from a version control repository.
How to collect HAProxy metrics
This article is a full tutorial on HAProxy monitoring and the best tools to get it done right. We will be looking into how to collect HAProxy metrics using a collectd daemon, push them into Graphite and visualize them in Grafana. To follow the steps in this blog, sign up for the MetricFire free trial, where you can use Graphite and Grafana directly in our platform.
Network Security: The Journey from Chewiness to Zero Trust Networking
Network security has changed a lot over the years, it had to. From wide open infrastructures to tightly controlled environments, the standard practices of network security have grown more and more sophisticated. This post will take us back in time to look at the journey that a typical network has been on over the past 15+ years. From a wide open, “chewy” network, all the way to zero trust networking. Let’s get started.
I used Rust in production for 6 months! Here's my feedback
Are you in two minds when it comes to learning new programming languages? Probably you may feel the same when you first heard about Rust programming language. Good things require some effort and here's what I have to say after using Rust programming language in production for a 6-month duration – It is great and Simply superb! Let's get the clear practical experience picture with Rust at Qovery.