Operations | Monitoring | ITSM | DevOps | Cloud
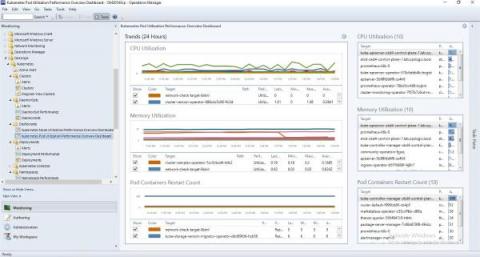
NiCE Active 365 Management Pack 4.1 released
Microsoft 365 services help companies worldwide improve business and revenue by providing best in class digital workspace experience. The NiCE Active 365 Management Pack complements this by advanced M365 monitoring such as full Teams Call analysis integrated into Microsoft SCOM. Advanced monitoring and analytics help you reveal unwanted micro-events influencing the health and performance of the system and its users.
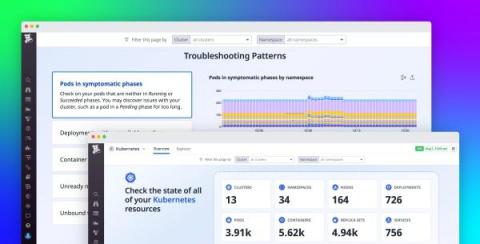
Equip any user to monitor Kubernetes with the Overview Page
Many organizations use Kubernetes to orchestrate their containerized applications. But because Kubernetes is complex, application developers may take some time to ramp up on the intricacies of monitoring a Kubernetes environment. This means that teams often need to create internal documentation and offer hands-on training to bridge the knowledge gap.
How Ekopak Manages Water Treatment Data with InfluxDB
A wide variety of industrial processes rely on water, and before it can be used, it needs to be treated to remove dissolved substances. Minerals have to be filtered out so they don’t form scales on equipment as water is heated and cooled, and bacteria needs to be removed in cases involving human health. Ekopak is a Belgian company working to make water treatment more sustainable by using less water and energy where possible.
Monitor Ruby Application Performance with Magic Dashboards
Application teams must understand what their customer experience is like. This is true not only from a general perspective (in terms of usability and responsiveness) but also on a day-to-day, minute-by-minute basis. In particular, when you work with distributed systems, errors are inevitable. Site traffic fluctuates throughout the day, and any one of a system’s dependencies could also encounter an issue at any time.
RESOLVE '22: Warp speed to digital innovation
The pandemic accelerated digital transformation in the business world by forcing companies to double down on areas in which they’d already begun investing. The mass move to video conferencing solutions in industries such as healthcare and education are two examples. In other industries, companies were only able to survive by jumping into completely new areas: brick-and-mortar retailers diving feet-first into e-commerce after lockdowns and health concerns kept shoppers indoors, for example.
Debunking 4 Cybersecurity Myths About Machine Learning
Machine learning has infiltrated the world of security tooling over the last five years. That’s part of a broader shift in the overall software market, where seemingly every product is claiming to have some level of machine learning. You almost have to if you want your product to be considered a modern software solution. This is particularly true in the security industry, where snake oil salesmen are very pervasive and vendors typically aren’t asked to vigorously defend their claims.
Observability: You Can't Buy It, You Must Build It!
In Part 1 of this series, we talked about the origins of observability and why you need it. In this blog (Part 2), we will cover exactly what observability is, what it isn’t, and how to get started. Before we can dive into how to approach observability, let’s get one thing clear: You can’t buy a one-size-fits-all observability solution.
Why Is IoT in Asset Management Solution Getting Popular Among Organizations?
These days technology is essential for businesses as their clients only want the best technology. Moreover, competition is high and having the best technology is significant for running daily operations successfully. Therefore, when an organization is equipped with a lot of assets in order to keep them maintained. In the market, there are several technologies available for effective asset management such as Barcode, QR Code, RFID, GPS, BLE, NFC, IoT, etc.