Operations | Monitoring | ITSM | DevOps | Cloud
Startup and running configuration management
Configurations are considered the heart of network infrastructure. They are often adjusted to improve the overall workflow of the network environment. One small unnecessary change to a configuration can bring down an enterprise’s entire network infrastructure. Therefore, the changes made to configurations must always be checked to ensure they are in sync with the devices to improve efficiency and performance. A network configuration is generally divided into two parts: 1.
SaaS Companies Are Reporting Weaker Margins Than They Need To - Here's Why
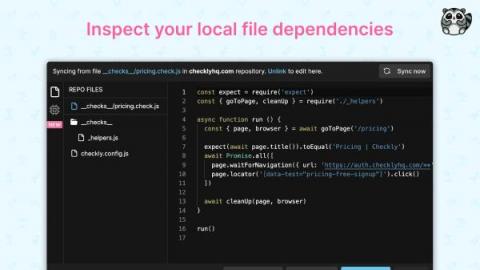
Checkly GitHub Sync Goes into GA
Welcome to the last day of our first Checkly Launch Week! We already talked about security, our new Playwright test runner and alert enhancements. Today, I’m delighted to announce that GitHub Sync is going into general availability (GA)! This post goes into the following topics.
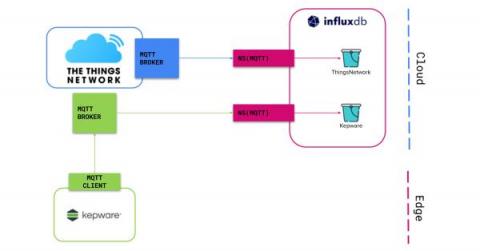
InfluxDB Cloud Native Collectors, Enterprise and Industrial IoT Examples - Part 2
Learn how to deploy InfluxDB Cloud’s Native Collectors with Kepware and the Things Network. In Part 1 of the blog series, we discussed connecting Kepware to InfluxDB using the new InfluxDB Cloud feature Native Collectors! As promised, let’s now discuss how to connect an Enterprise IoT platform, The Things Network to InfluxDB. Before we get to the juicy tutorial let’s run through a quick reminder.
EKS Cost Optimization: 7 Best Practices To Apply Immediately
What is 'Current' with data streaming?
6 Best Patch Management Software for MSPs and Internal IT
There is an increasing amount of technology used by businesses, from applications to entire networks. More technology means that there are more opportunities for errors or vulnerabilities in these systems to be exploited. With all those opportunities, it’s no wonder why these technological errors continue to be exploited by experienced hackers. What’s worse is that, according to Ponemon, 37% of businesses aren’t even scanning their IT environment for these vulnerabilities.
How to Get a Unified IT Asset Inventory in 24 Hours
What is Synthetic Monitoring?
No matter your business's sector or size, you probably depend on your websites, web applications, APIs, and complete IT infrastructure to be functional, available, and provide users with a pleasant experience. However, we are aware that websites and applications cannot just be set up and left alone.