Operations | Monitoring | ITSM | DevOps | Cloud
Enable Global DevSecOps with Cloud Enterprise and Xray on AWS
When software can travel around the globe at the speed of the cloud’s gusts, enterprises need to be extra certain the updates they release are safe for customers to use. If an app built in Palo Alto uses a vulnerable package from Belgrade, losses can ripple from Sheboygan to Shanghai. At JFrog, we believe enabling global DevSecOps in the cloud should be an easy process.
What's New: Related Incidents, Business Response, Mobile Status Dashboard, & New Integrations
An always-on world requires a proactive and preventative approach to managing your digital operations. PagerDuty is proud to announce our latest release, which helps streamline remote remediation by providing an at-a-glance overview of your system’s health. While we’re known for on-call management and incident response, PagerDuty does much more, including providing visibility into the business impact of an incident.
HoneyByte: Incremental Instrumentation Beyond the Beeline
“It turns out,” said Liz, “it was not a giant pile of work to start adding those rich instrumentation spans as you need them.” Liz Fong-Jones was telling dev.to’s Molly Struve about an error she encountered while trying to update her dev.to profile. When she entered honeycomb.io into the Employer URL field, the app responded with an angry red box...
Elastic: Distributed by design
As COVID-19 continues to make clear, being adaptable and resilient when the world changes can help a business stay alive. At Elastic, we know from experience that being distributed helps build a strong company that can scale and adapt as new challenges arise. In the spirit of open source and our relationship with the Elastic community, we’ve been offering tips and tricks on our blog and on social media about how to work effectively while remote.
Smooth mocking with the Elasticsearch Node.js client
A classic problem that every backend developer has faced during their work is testing an application that uses a database. A perfectly valid solution is to use the real database for testing your application, but you would be doing an integration test, while you want a unit test. There are many ways to solve this problem. You could create the database with docker, or use an in-memory compatible one, but if you are writing unit tests that can be easily parallelized this will become quite uncomfortable.
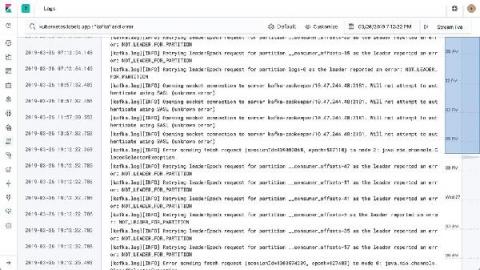
Extracting Insights from Metrics with AIOps for Better Observability
In this second installment of this blog series, we’ll discuss the importance of analyzing metrics, and how AIOps helps you with this fundamental pillar of observability. Without proper metrics analysis, you’re left blind to potential outages, or possibly worse — inundated with false positive anomalies, leading to alert fatigue and ultimately business impacts. Automated discovery and analysis can’t be achieved with legacy tools nor will it scale with humans.
PowerShell and 'Fileless Attacks'
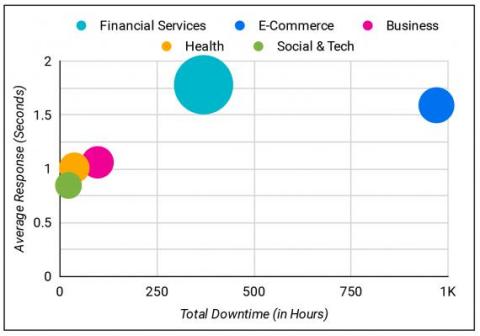
The Uptime.com Report for 2019
Unplanned downtime can drive significant losses in the form of unrealized revenue. Teams may be caught off guard, or may face an outage outside their control, extending downtime hours unnecessarily. Without automated monitoring and alerting, teams face undetected outages that silently threaten SLA fulfillment. The recommendations in this report are best used as a guide on what trends may drive Site Reliability Engineering in the near term.
Five worthy reads: Implementing a successful remote work environment
Five worthy reads is a regular column on five noteworthy items we’ve discovered while researching trending and timeless topics. This week, we delve into how organizations are increasingly adopting a remote work model, and how they can equip themselves to build a synchronized virtual workspace. In the wake of COVID-19 and the subsequent mandates to stay at home, many organizations have implemented a remote work environment in order to maintain business operations.