Operations | Monitoring | ITSM | DevOps | Cloud
Security
The latest News and Information on CyberSecurity for Applications, Services and Infrastructure, and related technologies.
Your team is running containers, but are they secure?
Organizations are modernizing IT infrastructure, restructuring teams, and accelerating application delivery with containers and Kubernetes. As with any technology, organizations are at various places within their journey. However, according to Gartner, more than 75% of global organizations will be running containerized apps in production by 2022. Chances are your team is using containers for some applications.
Introducing CFEngine Custom Promise Types
In CFEngine 3.17, custom promise types were introduced. This allows you to extend policy language, managing resources which don’t have built in promise types. The implementation of custom promise types is open source, and available in both CFEngine Enterprise and CFEngine Community. To implement a new custom promise type, you need a promise module.
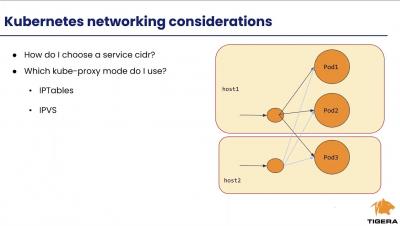
Deploying Calico in Your On-prem Kubernetes Cluster: Networking and Security Considerations
Integrating Security Across Clouds
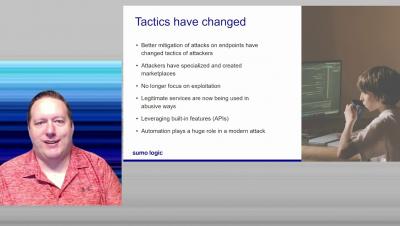
Emerging threats: a view from the front lines
Securing a Cloud Service with Sumo - From Compliance & Security Analytics to Production App Security
CISA's recommendations on how to recognize and avoid email scams
How to secure your network from a Ryuk ransomware attack
Universal Health Services (UHS), a Fortune 500 company and healthcare services provider, has reportedly shut down systems at facilities throughout the United States after the Ryuk ransomware hit its network on September 27, according to an article on the Health IT Security website. What is Ryuk ransomware? Ryuk is a sophisticated ransomware threat that targets businesses, hospitals, and government institutions across the world.