Operations | Monitoring | ITSM | DevOps | Cloud
Virtual Meetup: Building a COVID-19 Dashboard for Non-Programmers + Inside the COVID-19 data
Virtual Meetup: Multilingual Data & Search - Solving the Common Problems
Remote Work: Enhancing productivity and ensuring productivity.
Mastering website monitoring with Applications Manager
In the digital era, most enterprises use a web platform to reach potential customers and showcase the products or solutions they offer. Websites have become extremely popular as a medium of establishing a brand image, and they contribute in making a major share of revenue. Well-planned websites can capture the attention of the target audience, increasing the probability of them turning into valuable, paying customers.
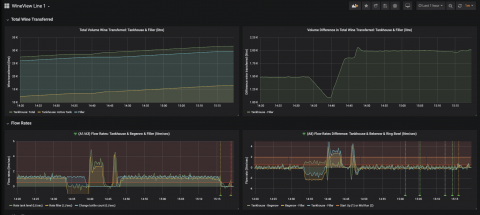
How ML6 used Grafana to deliver a 200% ROI for Accolade Wines
Did you know that Grafana pairs well with a fine wine? That’s what machine learning company ML6 discovered when they worked with their client Accolade Wines, an award-winning Australian vintner whose goal was to decrease the waste produced in its global operations. “Accolade Wines is really focused on being as efficient as possible,” says Rebecca Brooke, ML6’s team leader in the U.K. “They’re always looking at minimizing their environmental impact.”
Is the role of ITSM only limited to IT? Understanding Enterprise Service Management
Enterprises are facing new challenges not just in terms of staying relevant in the market and customers but also in controlling internal organizational chaos. Over the years, there have been a number of frameworks and models that were consistently being rolled out to assist enterprises to declutter operational and organizational challenges, streamline enterprise services and service delivery, and identify loopholes and fix them.
PagerTree Routing Rules
Tyto Care: Accelerating Telehealth in the Fight against COVID-19
At Logz.io, our team has the opportunity to partner with many cutting edge technology companies and products from different trades. Many have a crucial mission and help save lives worldwide. In the fight against the novel coronavirus, telehealth is one such sector. It compels us to do all we can to support these organizations by improving application accessibility and performance for users who need it. One of our customers epitomizes this—Tyto Care. Tyto Care is a healthcare pioneer.