Operations | Monitoring | ITSM | DevOps | Cloud
Debugging in production with Stackdriver Debugger - Stack Doctor
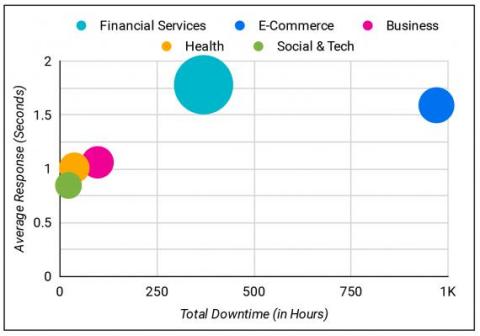
The Uptime.com Report for 2019
Unplanned downtime can drive significant losses in the form of unrealized revenue. Teams may be caught off guard, or may face an outage outside their control, extending downtime hours unnecessarily. Without automated monitoring and alerting, teams face undetected outages that silently threaten SLA fulfillment. The recommendations in this report are best used as a guide on what trends may drive Site Reliability Engineering in the near term.
Five worthy reads: Implementing a successful remote work environment
Five worthy reads is a regular column on five noteworthy items we’ve discovered while researching trending and timeless topics. This week, we delve into how organizations are increasingly adopting a remote work model, and how they can equip themselves to build a synchronized virtual workspace. In the wake of COVID-19 and the subsequent mandates to stay at home, many organizations have implemented a remote work environment in order to maintain business operations.
CloudWisdom - Demo of Performance Monitoring
CloudWisdom - Demo of Cost Management
Data Driven Dashboards with Kibana and Elasticsearch
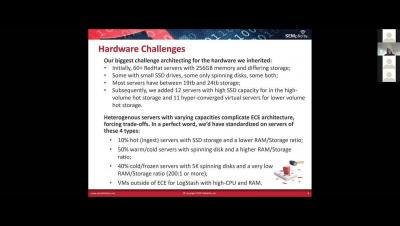
SEMplicity: Scaling Large ECE Deployments
Virtual Meetup: Elastic Workplace Search-Finding Where That Document Went
Webinar: Serverless At Scale: the Present and Future of Modern Cloud Architectures
In this webinar on 16 April 2020 we covered the following topics:
- The main challenges of scaling modern cloud applications
- Implementing well-architected best practices
- Battle-tested architectural patterns
- How to improve resilience and scalability