Operations | Monitoring | ITSM | DevOps | Cloud
Atlassian ITSM Demo Series | Incident Management
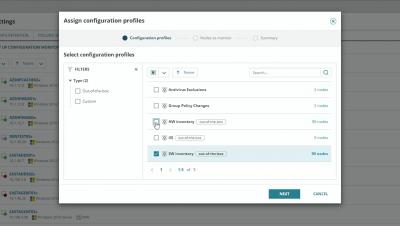
How to Monitor Changes to Hardware and Software Configurations
[KubeCon Recap] Cloud Native Architecture: Monoliths or Microservices?
Microservices have been gaining popularity since they were introduced in 2015. But they come with challenges for both developers and users because of the intricate configuration and deployment which often leave developers longing for the simplicity of monolithic applications.
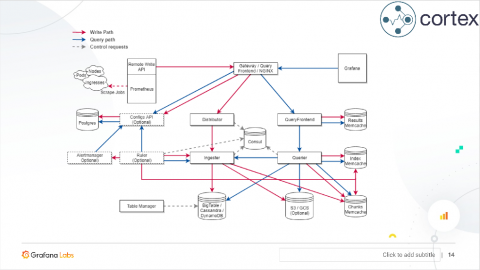
Unleashing a Better Open Source: Introducing Logz.io Cloud Observability Platform
Today, I am proud to announce the release of Logz.io Infrastructure Monitoring, a Grafana-based monitoring solution that enables engineers to speed up detection and reduce time to resolution. This new offering extends our Log Management and Cloud Security (Cloud SIEM) products, which together form Logz.io’s new Cloud Observability Platform.
Coffee break: SCOM v Azure Monitor, The Big Debate
“SCOM is dead” is a refrain often heard these days, in large part thanks to Microsoft’s latest marketing push on Azure Monitor. Luckily for you, that's fake news! Contrary to the view that Azure Monitor is fast replacing SCOM, the latter remains the most widely used monitoring tool today – and one that Microsoft remains invested in, as can be seen from SCOM 2019’s many new features. What is the real relationship between SCOM and Azure Monitor?