Operations | Monitoring | ITSM | DevOps | Cloud
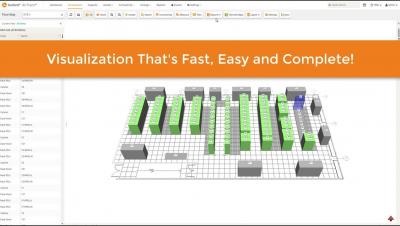
dcTrack 7 BI and Analytics
What is a post mortem incident? How can we monitor this?
In particular, I liked very much the article that our colleague Sara Martin wrote in Pandora FMS blog about crisis management in information technology, these are the steps: Legend: “Jack’s Lantern (https://commons.wikimedia.org/wiki/File:Jack-o-lantern.svg) This article starts from point number five: when after a certain time of recovery the crisis has been solved and becomes a post mortem incident. This word comes from the Latin language and it means “after death”.
How to Manage a Critical Incident
Critical incidents don’t come with a predetermined schedule or warning. So, it’s up to your organization to have an incident response procedure in place to combat these crises. Don’t have one? Read below to perfect your incident response operations and adopt the right tools and procedures to fight against any critical event.
The Future of IT Operations is Agile
Reinvention is the key to modern IT operations in a DevOps world. Headline after headline after headline tells the same story: Modern IT operations is an exercise in managing complexity. As the IT ecosystem increases in flexibility, scalability, agility, and possibility, the IT operations management workload is becoming increasingly unruly.
What Does Wi-Fi 6 Mean for MSPs?
Good IT Support? Or Just a Pain In The Bits?
Good IT Support is harder to pin down than you’d think but deciding which technology is better than the next is pretty straightforward for most of us. Who wouldn’t pick the latest iPhone or Android device over a flip-phone? Actually, most senior citizens—but to their credit flip-phones never really die, they just regenerate into larger flip-phones. Bad example. Point is we can rate, compare, trial, and study just about every digital technology on the market.
October 2019 Update: Improved usability and new emergency alarm triggering in the app
The October update of the mobile app includes the improvements described below and the user experience includes a new feature. The user interface of the app has been improved so that you can now decide for yourself if you want to see all Signls on the dashboard differentiated by categories. Using the “More” button on the dashboard’s Signl widget, you can now open a context menu and show or hide the display of the categories.
How to Keep Malware Out of Your Printers
The landscape of cybersecurity is always changing, and new threats are constantly emerging. One of the newest – and the most interesting, if you are into that kind of thing – is the rise of printer malware. This type of malware started to be reported in November 2017, when Barracuda Labs saw an attack where cybercriminals spoofed a printer to send a malicious attachment that appeared to be a legitimate file sent by a network printer.
Visualizing Sensu Go data in Grafana
Monitoring systems is critical to any IT operation. For many companies, these systems are a critical business component that can have serious business impact (including expensive downtime) if these systems fail. For this reason, it is essential that you have a good monitoring system in place that you can rely on, one that notifies you early if unforeseen problems occur.