Walkthrough to Set Up the Deep Learning Toolkit for Splunk with Amazon EKS
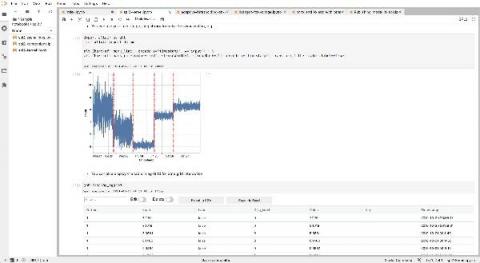
The Splunk Deep Learning Toolkit (DLTK) is a very powerful tool that allows you to offload compute resources to external container environments. Additionally, you can use GPU or SPARK environments. In last Splunk blog post, The Power of Deep Learning Analytics and GPU Acceleration, you can learn more about building a GPU-based environment. Splunk DLTK supports Docker as well as Kubernetes and OpenShift as container environments.