Operations | Monitoring | ITSM | DevOps | Cloud
How Endpoint Monitoring Saved My Life (Or At Least My Sanity)
Catchpoint makes parenting a saner sport! OK, that’s not the usual use case. But much as I know it sounds crazy, I used Endpoint Monitoring to explain to my 11-year-old gamer that I’m totally innocent. The reason she is having gaming lag and lost connections is not because of her parents’ poor home Wi-Fi or her old PC – and she doesn’t just have to take my word for it. Here, let me explain.
PagerDuty: Helping Every Business Move to Digital
Last year, businesses started focusing more on accelerating digital transformation initiatives to meet growing customer expectations and deliver consistent digital experiences from anywhere—no matter the product, service, or industry. PagerDuty partners with thousands of organizations to help reimagine digital operations and deliver real-time, digital experiences to their customers when it matters most.
Do you already know what Synthetic Transaction Monitoring is?
Most of us who work in IT understand the concept of basic monitoring. It is not that it is an irrelevant concept, but rather, it is essential for any infrastructure, either manual, by reading logs and checking machines and services; semi-automated, using custom-made scripts or, the safest and most recommended, using a specific tool such as Pandora FMS to centralize your monitoring. But what is synthetic monitoring? We will see that throughout this article.
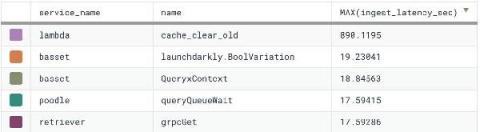
Event Latency: What It Is and Why You Should Care
Recently, we added a new derived column function to Honeycomb, INGEST_TIMESTAMP(), which can help customers debug event latency and/or inaccurate timestamps. A meaningful minority of the events sent to Honeycomb are already old when they arrive, and a very special few claim to have been sent from the future. Has this happened to you? Let’s do an experiment.
Detecting Cobalt Strike with memory signatures
At Elastic Security, we approach the challenge of threat detection with various methods. Traditionally, we have focused on machine learning models and behaviors. These two methods are powerful because they can detect never-before-seen malware. Historically, we’ve felt that signatures are too easily evaded, but we also recognize that ease of evasion is only one of many factors to consider.
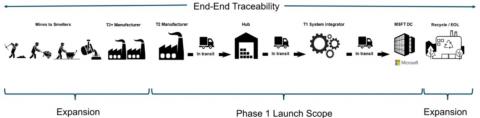
How Microsoft Used Splunk's Ethlogger to Turn Blockchain Data Into Supply Chain Insight
The way we ‘data’ is about to change, and Splunk’s Connect for Ethereum (aka EthLogger) is helping organizations to adapt. Splunk Connect for Ethereum enables organizations of all sizes to investigate, monitor, analyze and act upon their rapidly growing blockchain data sets across multiple chains.
Getting Started with OpenTelemetry .NET and OpenTelemetry Java v1.0.0
Recently we announced in our blog post, "The OpenTelemetry Tracing Specification Reaches 1.0.0!," that OpenTelemetry tracing specifications reached v1.0.0 — offering long-term stability guarantees for the tracing portion of the OpenTelemetry clients. Today we’re excited to share that the first of the language-specific APIs and SDKs have reached v1.0.0 starting with OpenTelemetry Java and OpenTelemetry .NET.
Network Throughput vs Bandwidth and How to Measure It
Running an open source multi-cloud with Ubuntu, LXD, and Mist
One of the advantages that Ubuntu brings to the cloud equation is improving an organization’s ability to run in multiple clouds. Running containers on top of Ubuntu further increases portability. Mist is an open-source multi-cloud management platform that helps teams centrally manage and control their Ubuntu instances across many different cloud environments and/or bare metal. This removes some of the operational and financial barriers to running applications in multiple clouds.