Operations | Monitoring | ITSM | DevOps | Cloud
Everything you need to know about .NET 5.0
If you’re a developer of .NET supporting enterprise apps developed in the .NET framework, you should know how the .NET 5 would impact your current enterprise app. Moving forward, there will be only one .NET to target macOS, Windows, Linux, iOS, Android, and more. Along with the release, there are new .NET APIs, language features, and runtime capabilities. The look and feel of the code and project files in .NET 5 would be the same, regardless of the type of app being created.
Cracked - 5 Annoying Compliance Problems for IT & Flexible Work
Are most companies right now thinking ‘everybody back to the office’, or ‘remote work forever’? My guess is neither. There is still too much uncertainty for businesses to lean heavily towards one option or the other. Instead, flexible work makes the most practical sense right now and I imagine that won’t change for some time. Yet, with flexible work can come plenty of compliance problems that can frustrate even the most agile and experienced of IT departments.
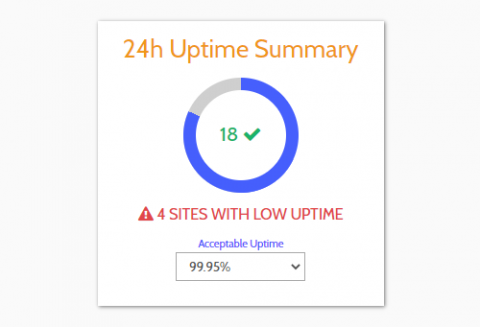
Stats At A Glance
We've just rolled out another new feature: a 'Stats Overview' area where you can view a summary of the stats for all your monitors at a glance. There have been several requests for this feature from customers who want to view the most important stats for their websites in one place. Here are the details...
Meet the new Monitive
Monitor HiveMQ with Datadog
HiveMQ is an open source MQTT-compliant broker for enterprise-scale IoT environments that lets you reliably and securely transfer data between connected devices and downstream applications and services. With HiveMQ, you can provision horizontally scalable broker clusters in order to achieve maximum message throughput and prevent single points of failure.