Operations | Monitoring | ITSM | DevOps | Cloud
Monitor SQL Server and Azure managed databases with Datadog DBM
Datadog Database Monitoring (DBM) provides comprehensive visibility into SQL queries running on your databases. Using DBM, you can troubleshoot database performance issues by drilling into frequently used queries and analyzing historical trends in your queries’ metrics and execution plans. Whether you operate self-hosted SQL Server instances or leverage Azure’s fully managed services, DBM can provide deep visibility into the databases your application depends on.
Setup RabbitMQ in HA Mode using Kubernetes Operator
Organizations are moving from monolithic architecture (where all the code building the application exists as a single, monolithic entity) to microservices architecture as it simplifies app management, making it easier to build, deploy, update, test and scale each service independently without affecting other parts of the architecture.
Upsun announces $140m series D round of funding
Qovery revival: Brand New Web Console for a world new Developer Experience
How IT Operations can demonstrate business value with Unified Analytics
As an IT Ops exec, imagine your jubilation upon learning that after a year of hard work across your NOC, DevOps and SRE teams, you are able to automate incident response by 25%. You’re elated as you enter your CTO’s office to share this information, and their response is.
Monitorama 2022 - A Q&A with Mehdi Daoudi
This year's Monitorama is quickly approaching. This year, the event is hosted in Portland, Oregon, from June 27 to 29th. It features talks from industry experts and community leaders on all things monitoring, observability, SLI/SLO, and most importantly, what practitioners are doing (not vendors and providers).
Multicloud Cost Management
More enterprises are adopting cloud computing to ensure that they can accelerate innovation, stay competitive, and enjoy cost savings. This trend has only increased in the last two years with the rise of remote work necessitated by the COVID-19 pandemic. With the rise of cloud adoption, multi-cloud and hybrid cloud deployments are increasing in popularity as well. According to a Gartner survey, 81% of survey respondents are using two or more cloud providers.
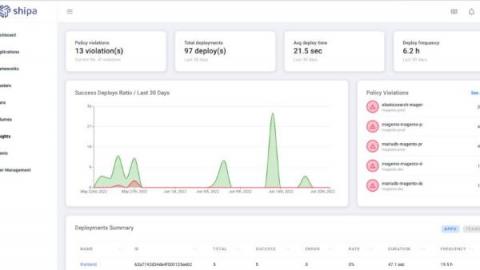
Are your applications secure? Can you find it out without complex rules?
The modernization of infrastructure and applications is driving the rapid growth of containers, and as companies scale the adoption of Kubernetes, it’s critical to incorporate security and compliance. The challenge? Compliance and security is a journey, not a state in time, and application security in Kubernetes has a large surface area. This challenge increases exponentially as you run more applications, onboard more developers, add more environments, add new pipelines, and more.