Operations | Monitoring | ITSM | DevOps | Cloud
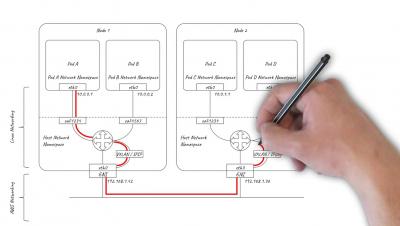
Everything you need to know about Kubernetes pod networking on AWS
Squadcast: Incident Resolution, The SRE Way
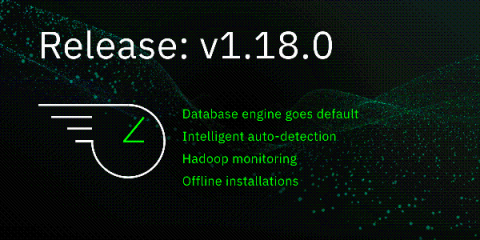
Release 1.18: What's new with the database engine?
As your infrastructure grows more complex, storing long-term metrics becomes difficult and costly to retain. Your team stars to limit the amount of historical data they archive, causing gaps in coverage. Anomalies start to slip through the cracks. Version 1.18 of Netdata aims to solve the monitoring metrics storage problem once and for all. Aside from 5 new collectors, 16 bug fixes, 27 improvements, and 20 documentation updates, here’s what you need to know.
Compliance Made Easy with JFrog Xray
As compliance managers, we often find ourselves in a struggle. Our responsibility is to uphold compliance standards but in order to achieve this, we need to “sell” the concept to the relevant stakeholders, inter alia the business teams and R&D. We’re put in the position of justifying required changes and processes and are thus mistakenly perceived as business “stoppers” and not enablers.
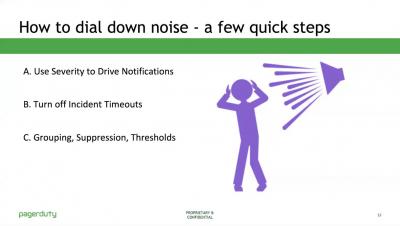
Making the Most of PagerDuty + Datadog
For your team to effectively respond to incidents, you need a shared, unambiguous incident definition so you can recognize when an incident has occurred and assign the appropriate severity. Definitions of an incident differ across teams, but whatever definition you use, identifying and monitoring key service level indicators (SLIs) can help you understand when your service is operating normally—and when its performance has degraded to the point where you need to trigger an incident.
OpsRamp Fall 2019 Release: Deliver Better Uptime with Service-Centric AIOps and Enable Compelling Customer Experiences With Multi-Cloud Monitoring
The OpsRamp Fall 2019 Release delivers comprehensive features for hybrid infrastructure management with machine learning-powered intelligent correlation and multi-cloud monitoring support. The new release also offers enhanced synthetic monitoring capabilities and a new custom integration framework for sharing data with third-party IT management tools.
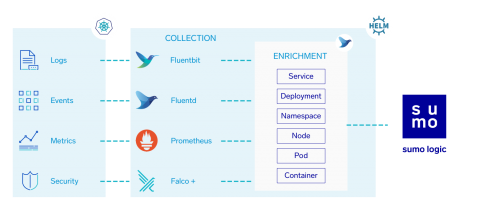
Kubernetes DevSecOps with Sumo Logic
With Sumo Logic, we can put all of these pieces together to build end-to-end Observability in Kubernetes.
REST vs. SOAP: Which is Better for Web Services?
Ask two developers whether SOAP (Simple Object Access Protocol) or REST (Representational State Transfer) is better for accessing web services and you’ll likely get two different answers – and maybe more. It’s a passionate debate, but the reality is that the best solution depends on the application. Let’s take a look at these two options and discuss the main pros and cons.
Threat Intelligence And Log Management: Security Through Automation
The constant evolution of security threats has long-since made preventing cyber-attacks and network intrusion attempts a nearly impossible task. Real threats are often hard to identify among a multitude of false alarms, and many experts understand that a well-integrated and fully-automated threat intelligence strategy is the best approach. Nevertheless, 70% of security industry professionals still believe threat intelligence to be too complex and bulky to provide actionable insights.