Operations | Monitoring | ITSM | DevOps | Cloud
How we identified clients with SSL certificates affected by Let's Encrypt mass-revocation
Yesterday, we sent out notifications to all our clients that are affected by the Let's Encrypt mass revocation of SSL certificates. In this post, we'll share the details how we found those certificates. Now, the morning after, we're well rested and in good shape to do a proper write-up on the matter.
Resolve Insights Integration with Cherwell
3 Things We Learned from EMA About AIOps and the Automation Handshake
AIOps is the trendy cool new kid on the block in the IT operations world. No doubt about it. However, with all the buzz surrounding AIOps, it’s easy to skip over some of the basics. How many IT operations professionals can clearly define what AIOps is? Beyond the baseline definition, why should you care? What about plugging it into your existing automation and analytics ecosystem?
Asset Management On-Boarding and Off-Boarding Users: 3 Keys to an Off-Boarding Process
A friend of mine recently shared an experience with me that he had while working as a manager for a software manufacturer. The experience was about an employee he had to terminate. He told me that after meeting with the employee and HR, he completed the paperwork that was required and sent it back to the HR department. Six months later, he received an email from finance giving him an overview of the expenses for his department.
Citrix SCOM Management Pack is Reaching EOL - eG Innovations Can Help!
Over 100 million users across 400,000 organizations use Citrix virtual apps and desktops technologies for accessing different types of business applications. There are many software products for monitoring the availability, performance, and usage of Citrix technologies. Of these, Microsoft SCOM is the most popular.
Pandora FMS and Toshiba: a success story in hospitality business
Pandora FMS and Toshiba met each other on a cold winter morning, they exchanged looks and… This would be a great start to a love story, wouldn’t it? However, the relationship between Pandora FMS and Toshiba has a different nature: teamwork. By now you know Pandora FMS, don’t you? That flexible and complete monitoring software, with which you can monitor all your devices, from networks, servers, UX, IoT, applications or business processes, to virtual environments, etc.
Elastic SIEM for home and small business: SIEM overview
Hello, security enthusiasts! This is part seven (can you believe it?) of the Elastic SIEM for home and small business blog series. If you haven’t read the first six blogs in the series, you may want to before going any further. In the prerequisite blogs we created our Elasticsearch Service deployment (part 1), secured access to our cluster by restricting privileges for users and Beats (part 2), then we created an ingest pipeline for GeoIP data and reviewed our Beats configurations (part 3).
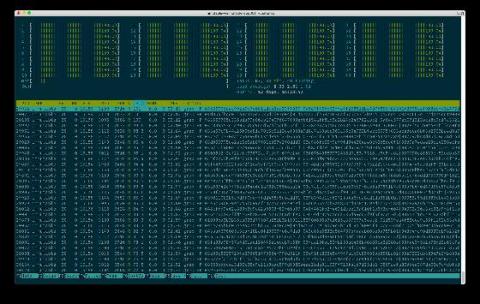
How to Check Website Logs
Have you ever looked at your website logs and realized they don’t make sense to you? Maybe your log levels have been abused, and now every log categorizes as “Error.” Or your logs fail to give clear information on what went wrong, or they reveal sensitive information that hackers may harvest. Fixing these problems is possible! Let’s explore how you can write meaningful log messages and use log levels correctly.
C# Exception Handling Best Practices
Welcome to Stackify’s guide to C# exception handling. Why is this topic so important? In modern languages like C#, “problems” are typically modeled using exceptions. Jeff Atwood (of StackOverflow fame) once called exceptions “the bread and butter of modern programming languages.” That should give you an idea of how important this construct is.