Operations | Monitoring | ITSM | DevOps | Cloud
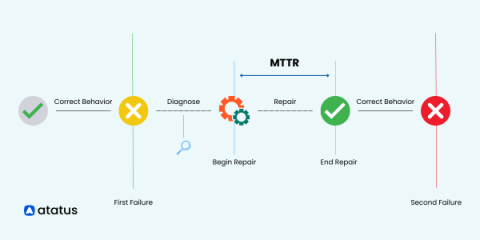
What is MTTR? Calculation and Reduction Strategies
In the fast-paced world of software development, every minute counts. When disruptions occur, whether there are minor or major system failures, organizations need to bounce back to maintain seamless operations. That's where MTTR (Mean Time to Repair) steps onto the stage as a game-changing metric. Are you ready to unlock the secrets behind reducing downtime, boosting performance, and ensuring software reliability?
Streamline Incident Response with Komodor and Squadcast
With the growing popularity of Kubernetes as a container orchestration platform powering the microservices revolution, comes greater complexity with managing, monitoring, and responding to incidents at scale. Challenges with real production environments include full visibility into your clusters and environment’s health, alongside real-time incident management and response.
Use incident cycle time to optimize your incident response process
Although the causes and solutions for incidents vary widely, most incidents follow a similar timeline from declaration to resolution. We call the period of time it takes to move from one phase or milestone of an incident to the next cycle time.
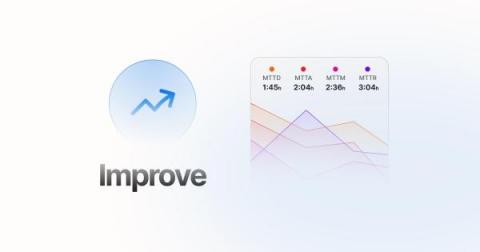
Understanding MTTR Networking: How to Improve Incident Response Time
As organizations continue to shift their operations to cloud networks, maintaining the performance and security of these systems becomes increasingly important. Read on to learn about incident management and the tools and strategies organizations can use to reduce MTTR and incident response times in their networks.
Why an incident response plan is a security must-have for every organization
“By failing to prepare, you are preparing to fail. Preparation prior to a breach is critical to reducing recovery time and costs.” (RSAConference) For 83% of companies, a cyber incident is just a matter of time (IBM). And when it does happen, it will cost the organization millions, coming in at a global average of $4.35 million per breach. The damage isn’t only financial, nor solely related to customer loyalty and brand equity.
PagerDuty Launches New Innovations to Reduce Tool Sprawl and Optimize Operations
The number of tools used by distributed teams to manage incidents has multiplied over the years, leading to a valley of tool sprawl. Throw in manual processes and you’ve got too much toil and multiple points of failure. Maintaining disparate tools and systems isn’t just unwieldy, it’s expensive. Our latest capabilities add to the PagerDuty Operations Cloud to make it easier than ever for teams to consolidate their incident management stack.
7 Types of Incident Response Tools
Incident response tools are software applications or platforms designed to assist security teams in identifying, managing, and resolving cybersecurity incidents. Incident response is a crucial part of an organization’s cybersecurity strategy, making it possible to detect threats, analyze vulnerabilities, respond to attacks, and recover from security breaches. Incident response tools are vital for safeguarding organizations against evolving cyber threats.
Why Automating IT Incident Response Matters for Financial Institutions
Last month, the Singapore bank DBS experienced a 10-hour outage of its digital services. Not only was it massively disruptive to customers, but it caused the bank’s stock to lose 1.4% of its value in a single day. And it’s not the first time DBS has had to deal with the fallout of an IT snafu; in November 2021, Singapore’s finance regulatory body imposed significant additional capital requirements on the bank after its digital banking services were disrupted for two days.
Don't Just React to Incidents-Prevent Them
Incident response has been the cornerstone of reliability for decades. From digging in the server logs to navigating modern observability dashboards, responding quickly to incidents and outages is a big part of minimizing downtime. And it should be! When something breaks, your team should move as quickly as possible to address and repair the problem.