Command Agents by iOPEX: Scaling Enterprises with Agentic AI
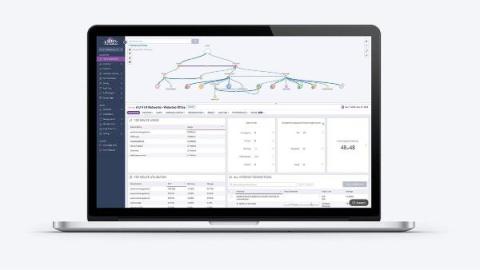
This video presents iOPEX’s Command Agents, powered by Agentic AI, which go beyond chatbots to autonomously detect, decide, and act. Integrated with ServiceNow, they deliver faster deployments, fewer errors, and higher productivity across key enterprise functions.