Operations | Monitoring | ITSM | DevOps | Cloud
Combating threats with UEBA: Money matters
In this four-part series, we explore hypothetical cyberattacks inspired by real-life events in four different industries: healthcare, finance, manufacturing, and education. We’ll take a look at unforeseen security attack scenarios, and discover how user and entity behavior analytics (UEBA) can be leveraged to safeguard organizations. In this second post of the series, we’ll examine cyberattacks that threaten the financial sector.
Roll up status from your Grafana dashboards to one big-picture view
Earlier this year, our partner GripMatix released a feature-packed Citrix management pack (MP) that helps improve the monitoring of Citrix environments using SCOM. This was warmly received by our customers who preferred not to shell out for the premium ‘Citrix Platinum’ license, and so don’t have access to SCOM MPs directly from Citrix.
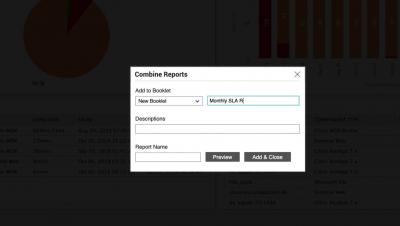
How To Combine and Schedule Multiple Reports
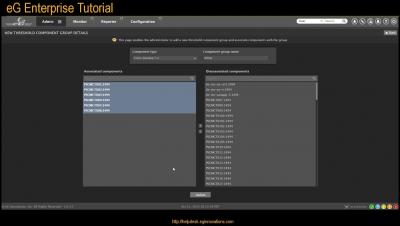
Creating Group Thresholds
Creating a User Journey Tutorial
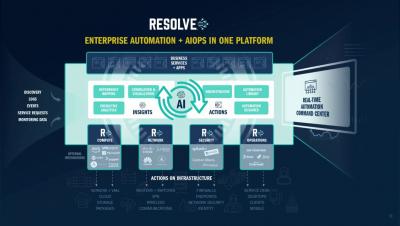
What happens when we combine AIOPS with IT Automation?
How DevOps Benefits from Application Performance Monitoring (APM)
Competition is a funny thing. To gain or keep an edge against your competitors, you may need to push the envelope to use newer technologies and processes. But done wrong, that very technology or process could lead to your ruin. This is where we are with DevOps. The methodology that became popular in the mid-to-late 2000s is embraced by many companies . Done the right way, it will help your organization challenge its competition to keep up with customer and user demands.
Why You Should Go Serverless for DevOps
Over the last decade, DevOps has become an important part of software engineering culture, influenced by the wide adoption of microservices, containers and cloud computing. A recent step in the evolution of cloud-based and microservice architecture is the serverless computing – a code execution model where the cloud provider takes total responsibility for the operating system and hardware management.
How Log Analytics Improves Your Zero Trust Security Model
Over the past few years, cloud computing has passed through its hype and early-adopter phases. Now we are hitting the peak of migration from on-premise to cloud-based infrastructure. Consequently, this transition and the advent of cloud computing has dramatically changed the way we think about security. Namely, the security paradigm has shifted towards a Zero Trust Security Model.