Operations | Monitoring | ITSM | DevOps | Cloud
How Verizon Achieved Automation and Self-Service with Grafana
Can you monitor us now? That was the question Verizon started asking as the Fortune 500 company expanded its portfolio beyond communications services to include brands such as Yahoo! and Huffpost. “We’re not just grandma’s landline,” Sean Thomas, Verizon Systems Engineering Manager, told the audience at GrafanaCon in L.A. “We’re not just your mobile provider. We are a media company. We have 5G solutions. We’re building technology.
Observability Through The Development Lifecycle
Cisco discusses benefits of VirtualWisdom with Cisco MDS 9000
The Art of the Late Start
There is a lot of dogma around shipping a product in startup land. Many founders follow strict patterns they got from a book or some influencer's tweet. "Ship Early" is one of the more stubborn ones, and in many cases it is exactly the right thing to do. The earlier you start learning about what your users' problems and how your product solves that, the better. I shipped Checkly fairly late.
5 mobile apps you can use for VoIP calls
The VoIP (Voice over Internet Protocol) phone system is not an alien technology in this progressive world. People have left behind the traditional landline telephony system long ago and now enjoy un-interrupted, crystal-clear and almost free calls over the Internet. VoIP technology is increasingly used by everyone whether it is an individual or a business organization. the technology has impressed a lot of audience by its versatility.
How to Search through LogDNA Archives
Retention is a crucial factor in adopting a log management solution. For most organizations, 30 days is a perfect balance between having to access historical log data and the high cost of storage. However, some organizations need to retain logs for a much longer period of time, whether it’s to comply with regulations, perform frequent audits, or monitor changes to operations over time.
Incorporating Crash Data Into Your Workflow
Crash reporting can alter the balance between support and development, and swing it in your favor! Sure "literally" is an overused term. But, I think it’s fair to say that “LITERALLY” nobody likes it when software crashes. Users don’t like it when the software they love using breaks. They’re left wondering what happened and how long will it be until there’s a fix.
8 Ways To Love Your Computer More
We consider ourselves tech savvy. If you are reading this blog, you probably do too. And like us, you probably expect that computers are just supposed to work for you. However, in my experience, this close relationship we share with our machines just expands the realm of possible annoyances we encounter. Here are some easy ways to help you improve your relationship with the most important piece of equipment in your working life.
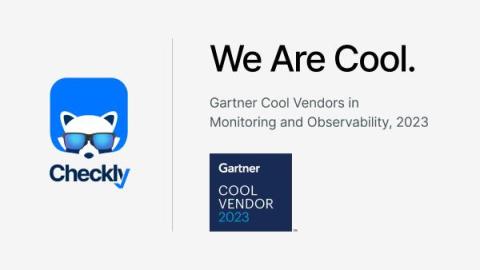
A Cool Milestone for Monitoring as Code: Checkly Recognized a THIRD Time by Gartner!
Hello, Checkly community and Monitoring as Code (MaC) aficionados! We have some exhilarating news that we can't wait to share. Our mascot is sporting sunglasses today because Checkly has been named in Gartner®'s 2023 Cool Vendors in Monitoring and Observability: Where Awareness Meets Understanding report!