Operations | Monitoring | ITSM | DevOps | Cloud
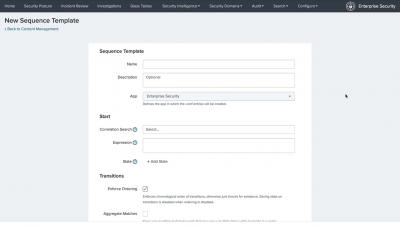
Splunk Enterprise Security: Event Sequencing
Using Audit Logs for Security and Compliance
Most software and systems generate audit logs. They are a means to examine what activities have occurred on the system and are typically used for diagnostic performance and error correction. System Administrators, network engineers, developers, and help desk personnel all use this data to aid them in their jobs and maintain system stability. Audit logs have also taken on new importance for cybersecurity and are often the basis of forensic analysis, security analysis, and criminal prosecution.
Kubernetes Cheat Sheet
Kubernetes is an open-source container-orchestration system for automating application deployment, scaling, and management. It was originally designed by Google, and is now maintained by the Cloud Native Computing Foundation.
3 Reasons Why Website Speed is More Important than Ever
Today’s business environment is relentlessly fast-paced. Today’s startups blast into tomorrow’s enterprises. And just as rapidly, today’s unicorns take a one-way journey into “hey, whatever happened to…” country. However, there’s another critical piece of the velocity puzzle that many businesses are missing, and it’s costing them customers and profits: the speed of their website.
The Age Of Simple Products And Even Simpler (If Any) UI
Moving further than design, a good interface is an invisible interface…
Top 10 Azure Cognitive Services
Microsoft’s cloud-based platform Azure has helped many businesses expand and cut back on their costs associated with hosting and storing data on a traditional server. Furthermore, the platform has given developers a chance to create, manage, and deploy powerful applications capable of assisting cloud customers to perform any number of tasks. From handwriting recognition to text sentiment analysis and Bing ad-free image search, Azure’s ML-based services spans many areas.
12 things you should know before recording your transactions
We want you to get started on the right foot when setting up your Web Application Monitoring, so we put together this list of 12 things for you to remember when recording your transactions.
September Launch Notes: APM, zipped source maps, and more
Raygun’s Launch Notes are your regular roundup of all the improvements we made to Raygun in the last month — from major feature releases to performance updates.
timeShift(GrafanaBuzz, 1w) Issue 64
This week the Grafana Labs team was busy prepping for the Grafana v5.3 stable release! Grafana v5.3 adds Stackdriver as a core datasource, a new graphical query editor for Postgres, enhancements to TV and kiosk mode, and a lot more. See the release section for a list of all the new features.