Operations | Monitoring | ITSM | DevOps | Cloud
Reputation Matters - Nexthink's Execs Share Favorite Customer Stories
Perhaps one of Nexthink’s most endearing qualities is that it has never been a “drink the kool-aid” type of company. Yes, we are proud to be the leading experience management platform in IT, but that honor is most championed from outside, not within. From its beginnings, Nexthink has been used by enterprise IT to narrow the gap between what employees expect at work and what they receive.
Logging for DevSecOps
Logging is probably not the first item to come to mind when most of us think about DevSecOps, a term that refers to the integration of security into DevOps processes, but it should be. Logging and log management play a critical role in helping to put DevSecOps principles into practice by ensuring that developers, IT operations staff, and security teams have the visibility and communication pipelines they need to prioritize security at all stages of the DevOps delivery cycle.
What is Logstash?
In this article, we are going to have a quick introduction to Logstash, a very popular application for collecting, processing and filtering log data – and see how it works. We will review plugins, installation and configuration of Logstash, we will briefly mention Beats, and also compare Logstash to other log collectors and review Logstash alternatives.
Lessons from the city of Copenhagen
Implementing change in large organizations is always a challenge, and the City of Copenhagen, with its 45,000 employees, is no exception. Three years ago, we embarked on a journey to implement a central enterprise service management portal using ServiceNow HR Service Delivery. Our objective was to improve the employee experience.
Splunk and the WEF - Working Together to Unlock the Potential of AI
Use of AI can be critical when developing systems to support social good, with some inspiring examples using Splunk in healthcare and higher education organisations. According to our State of Dark Data report, however, only 15% of organisations admit they are utilising AI solutions today due to lack of skills. So how can we help organisations unlock the potential of AI?
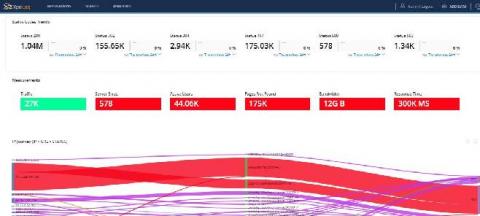
Using Observability as a Proxy for Customer Happiness
Today, users and customers are driven by response rates to their online requests. It’s no longer good enough to just have a request run to completion, it also has to fit within the perceived limits of “fast enough”. Yet, as we continue to build cloud-native applications with microservice architectures, driven by container orchestration like Kubernetes in public clouds, we need to understand the behavior of our system across all aspects, not just one.
How to Modernize Your Security Operations Center (SOC)
In an evolving world, the modernization of the security operations center (SOC) is pivotal to the success of digital transformation initiatives. Security teams, however, are facing a shortage of cybersecurity professionals and struggling to detect and prioritize high-priority threats. Analysts in data-driven organizations can combat these issues by bringing people, process and technology together.
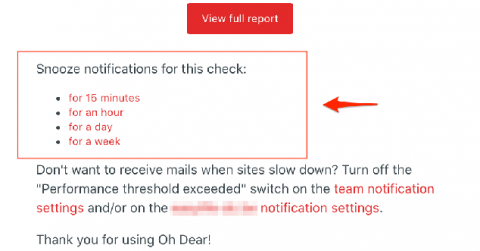
Adding action links to Oh Dear email notifications
Last week, we improved the email notifications sent by Oh Dear whenever something is down or broken. They now contain links that allow you to snooze further emails, essentially "silencing" the alert for a defined period of time.
July 2020, What's new? Qovery Business, Web Interface, Faster deployments
Hello and welcome to another issue of This Month in Qovery! Qovery helps developer to deploy their applications in the Cloud in just a few seconds. This is a monthly summary of its progress and community. Do you build something with Qovery? Do you want to be mentioned? Tweet us at @Qovery_ or reply to this email.