Operations | Monitoring | ITSM | DevOps | Cloud
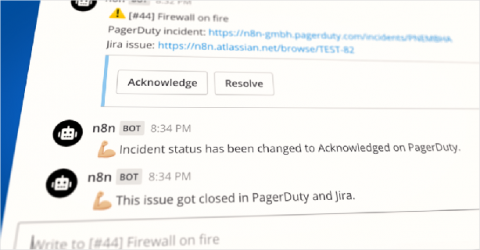
Creating powerful automations with n8n and Mattermost
Tanay is the Head of Developer Relations at n8n. He has published books on WebVR, virtual assistants on Raspberry Pi, and FirefoxOS. He has been listed in the about:credits of the Firefox web browser for his contributions to the different open source projects of the Mozilla Foundation. I’ve been involved in the DevOps world for a while and yet I finished reading The Phoenix Project only recently. The book piqued my interest in how teams execute their incident response playbooks.
StackState Open-source
Open-source software started around the millennium and is now one of the cornerstones of modern software development. Open-source projects make their source code available to anyone so that engineers across the world can inspect the code to find bugs or make changes to suit their needs. Today, there are more than 180,000 open-source projects available, according to Wikipedia. We at StackState are big believers in open-source software.
Blade servers vs rack servers. Fight!
Choosing between blade servers or those intended to go installed in a rack is a small headache that is repeated daily in the complex minds of technicians around the world. What configuration to choose? What can best serve my installation? These are questions that are repeated while they pull out their silvery and silky hairs.
How to easily correlate logs and APM traces for better observability
Application performance monitoring (APM) and logging both provide critical insight into your ecosystem. When paired together with context, they can provide vital clues on how to resolve problems with your applications. As the log data you analyze becomes more complex, navigating to the relevant pieces can be tricky using traditional tools. With Elastic Observability (powered by the Elastic Stack), correlating logs with APM is as simple as a few clicks in Kibana.
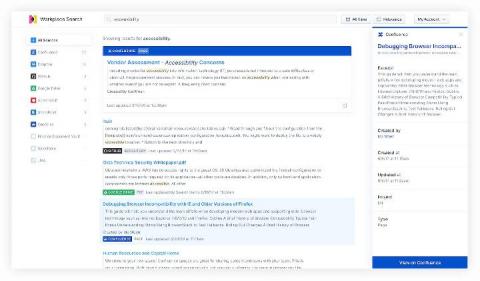
Searching Salesforce: Boosting your teams' productivity with Elastic Workplace Search
“If it’s not in Salesforce, it didn’t happen.” You’ve undoubtedly heard it, or perhaps you’ve said it yourself. And why not? Over the past 15 years, Salesforce has redefined the CRM industry, becoming the de facto solution for managing sales, customer service, marketing automation, and analytics functions with its cloud-only approach. As Salesforce’s solutions have expanded so has their user base.
Announcing Our Series A
It’s Friday at about quitting time, and my plans for the evening involved a great cocktail, hanging out with friends, and maybe continuing to binge The Office. Sadly, there was a problem. Our alerting system detected an enormous and immediate spike in errors. The error description was along the lines of “table ‘servers’ does not exist” and thousands of customers couldn’t use a large cloud provider’s services.
Spam In the Browser
What is Code Profiling? Learn the 3 Types of Code Profilers
At Stackify, we’re all about helping you improve your application’s performance. We have actually developed two code profilers ourselves. Because of that, we like to think we know a thing or two about code profiling. Today I want to talk about the three different types of code profilers, describe the differences between them, and recommend some tools for your toolbox.
Ubuntu 20.04 LTS to enforce stronger TLS v1.2 encryption by default
In Ubuntu 20.04 LTS, the OpenSSL 1.1.1f library has been modified to use Security Level 2 by default (previous versions of Ubuntu use Security Level 1). Security Level 2 guarantees that protocols, key exchange mechanisms, cipher suites, signature algorithms, certificates and key sizes provide a minimum of 112 bits of message secrecy. In practice, it means that RSA keys are required to be at least 2048 bits long and ECC keys at least 224 bits using the SHA256 certificate signature algorithm.