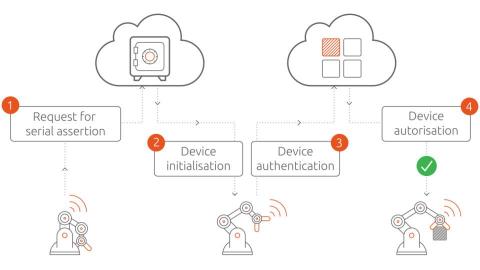
Cybersecurity defenses for IIoT
Cybersecurity attacks on industrial IoT solutions can have detrimental consequences. This is the case because IoT devices record privacy-sensitive data and control production assets. Therefore, demonstrable trustworthiness is prerequisite to IoT adoption in industrial settings. Fortunately, IT security is a mature field. Experts have identified classes of threats devices may be subject to. Let’s discuss these threat patterns and mitigation strategies in the IIoT context.