Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on Cloud monitoring, security and related technologies.
How to Implement FinOps Successfully - Episode 3
Now that you are starting to build your FinOps team and slowly changing your organizational culture, it’s time to start putting the teams to work - TOGETHER! In this blog I will provide you with some tools and processes to get you started.
Detect suspicious activity in GCP using audit logs
GCP audit logs are a powerful tool that track everything happening in your cloud infrastructure. By analyzing them, you can detect and react to threats. Modern cloud applications are not just virtual machines, containers, binaries, and data. When you migrated to the cloud, you accelerated the development of your apps and increased operational efficiency. But you also started using new assets in the cloud that need securing.
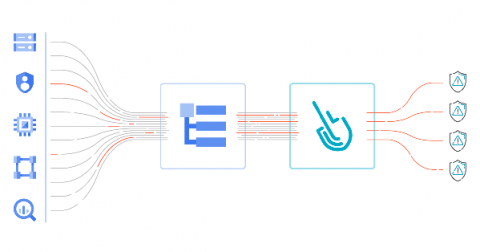
Cloud lateral movement: Breaking in through a vulnerable container
Lateral movement is a growing concern with cloud security. That is, once a piece of your cloud infrastructure is compromised, how far can an attacker reach? What often happens in famous attacks to Cloud environments is a vulnerable application that is publicly available can serve as an entry point. From there, attackers can try to move inside the cloud environment, trying to exfiltrate sensitive data or use the account for their own purpose, like crypto mining.
Why Your Business Should Consider Private And Direct Connections To Google Cloud
Using SQL Clone with Githooks & Branch Policies in Azure DevOps
5 hacks to create and deliver an effective Service Management [Cloud]
Boost Permissions Management with JFrog on Azure through Active Directory SSO
10 Mistakes to Avoid When Sizing Cloud Resources
One of the most common concerns when moving to the cloud is cost. Given that cloud allows you to turn IT costs from CAPEX (long-term investments ex. in hardware equipment and software licenses) into OPEX (day-to-day operating expenses), it’s crucial to choose the right service and estimate it properly. In this article, we’ll look at the common pitfalls and discuss how you can avoid them to truly benefit from the cloud’s elasticity.