Operations | Monitoring | ITSM | DevOps | Cloud
Kubernetes Master Class: Managing SQL Servers with Kubernetes
Looker - A single source of truth in multi-source world
WSUS: The outdated way of staying updated?
WSUS (Windows Server Update Service) is an add-on provided by Microsoft for patching Windows applications. Along with being free, the basic functionalities that WSUS provides makes it an easy choice for major SMBs. However, in reality, WSUS falls short in a number of ways; because of this, many teams that rely on WSUS for their patching needs end up investing in additional tools that usually come at an additional cost.
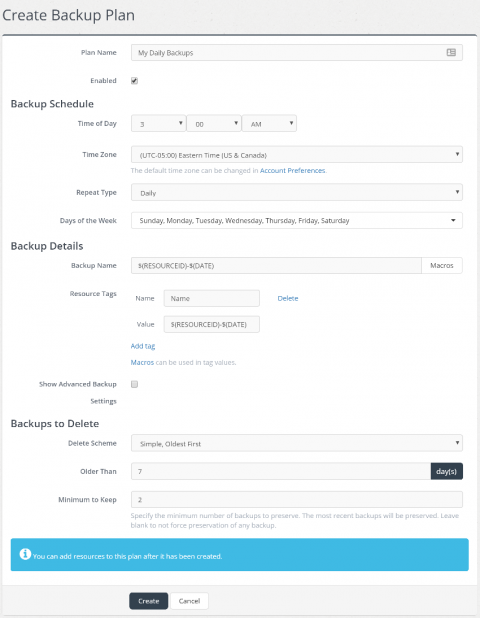
Introducing Managed Backups
Today, I’m happy to announce a significant new feature to Skeddly: Managed Backups. Once you have created your plan and added resources, Skeddly will create the necessary actions to create and delete those backups according to your desired schedules.
Resolve Introduces Expanded Global Partner Program to Deliver IT Automation to New Markets & Fuel Innovative Service Offerings
We are thrilled to announce the formal launch of our global partner program. This program will provide more routes to market for distributors and value-added resellers (VARs) and create new service opportunities for managed service providers (MSPs), systems integrators (SIs), and consulting partners.
Introducing a brand-new look for Statuspage
Here at Statuspage, we take pride in helping you communicate proactively to customers during a service outage. We also believe that during moments of stress times, the tools you rely on should be simple, intuitive, and easy to use. Using simplicity as our guide, we’ve updated the design of the Statuspage management portal. We kept things organized much as before, keeping the focus on what’s most important – helping you create and update incident communications.
Single Sign-On for Kubernetes: Dashboard Experience
Over my last two posts (part 1 and part 2), I have investigated user authentication in Kubernetes and how to create a single sign-on experience within the Kubernetes ecosystem. So far I have explained how Open ID Connect (OIDC) works, how to get started with OIDC and how to perform a login from the command line. The final piece of this puzzle is the Kubernetes dashboard, often used by our engineers alongside kubectl.
3 Layers to Defend Your Kubernetes Workloads
Researchers at Netflix and Google recently reported a vulnerability in the HTTP/2 protocol that enables adversaries to execute a DOS attack by legitimate use of the protocol. These types of attacks are very difficult to detect and mitigate because the traffic is valid HTTP/2 traffic. While HTTP/2 is a relatively new protocol it should be noted that even after several years of hardening we still see vulnerabilities for the TCP protocol like the recently reported SACK vulnerability.
5 Tips for getting the most out of AWS SAM
AWS introduced the Serverless Application Model (SAM) to ease the building of serverless applications on AWS. Essentially, it is an extension of AWS CloudFormation, and consists of two major components: SAM template specifications and SAM CLI. In this article, we’re going to share five tips to get the most out of AWS SAM templates. So, without further ado, let’s dive right in.