Operations | Monitoring | ITSM | DevOps | Cloud
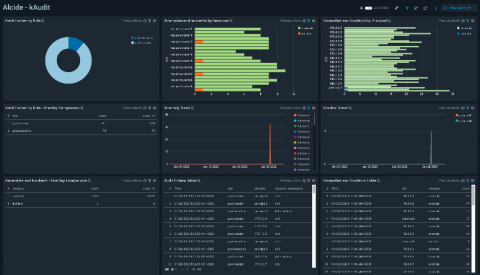
Alcide kAudit Integrates with Sumo Logic
What Is a Requirement Traceability Matrix?
When developing software applications, we want to make sure the application does what the software requirements say it’s supposed to do, and testing proves that it does. In this article, I’ll explore how to link requirements to test cases, and I’ll explain what a requirement traceability matrix is and how to build a simple one.
Migrating to Kubernetes
The reasons to move to Kubernetes are many and compelling. This post doesn’t make the case that you should migrate, but assumes you have already decided that you want to. When you’re clear on what you want to do and why you want to do it, the questions of “When?” and “How?” become your focus. What follows centers on the question of how to approach making Kubernetes the platform on which your workloads thrive.
Now on Now: A new line of defense
Some would liken the ServiceNow Security team to a silent, but highly skilled group of warriors working continuously to protect our customers and our services. To deliver that we have to ensure our company, people, and assets are secure. The fact is that our Security team is much more than that. They work tirelessly behind the scenes to constantly enrich ServiceNow’s security posture.
How Road Traffic Insights Derived from Sensor Data Improve Public Safety and Reduce Emergency Services Response Times
It’s easy to see the value of sensor data that enables acting in time. Just picture driving as the scene of a massive traffic accident unfolds and ambulances race to the rescue…what a difference a few seconds can make. What if past traffic patterns could help city operators predict and manage traffic flow at critical times?
Top 5 Cybersecurity Threats to Watch in 2020
These days, cybercriminals are ambitious and innovative, with no shortage of tools and resources at their disposal to go after high-stakes targets and execute malicious code — all while flying completely under the radar. To prepare you for what’s ahead, below are five of the top cybersecurity threats you might encounter in 2020.
Launching the Community COVID-19 Dashboard Project
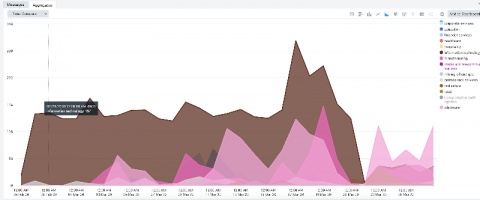
Let Data Shed Some Light in the Midst of Uncertainty The burden the COVID-19 novel coronavirus has placed on the world is enormous. There’s a great thirst for information and clarity. So, we at Logz.io have decided to offer a Community COVID-19 Dashboard Project, so that everyone can better understand how the outbreak impacts the world and their region. We see that as a community effort.
Why Cloud Cost Optimization is Ready to Shift Left (Just like Security Did)
Today, you probably wouldn’t blink at the idea of involving security in your development process. In fact, “shifting security left” has become so commonplace in the security industry, that there are conferences and job titles dedicated to SecOps (or DevSecOps or SecDevOps *eye roll emoji*). Yet, it wasn’t that long ago that the massive transition to this mindset took place.