Is your business PCI DSS compliant?
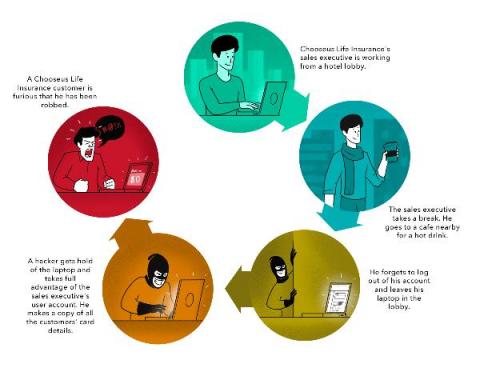
How Chooseus Life Insurance lost its customers’ cardholder details and their trust In August 2019, reporters began flocking to Chooseus Life Insurance’s head office in Detroit after news leaked that thousands of the company’s customers had lost money due to a security breach. The CEO of this life insurance company released the following statement: “We have had your trust for two years.