Operations | Monitoring | ITSM | DevOps | Cloud
Blog
Why Kubernetes Will Disappear
Over the last few months, I’ve been listening and involved in conversations about Kubernetes (k8s) and trying to identify the common topics that creates debate on whether it’s a “good” or “bad” idea. There are sensible points of view on both sides of the debate.
Gaining holistic visibility with Elastic Security
Let’s talk visibility for a moment. Security visibility is a data-at-scale problem. Searching, analyzing, and processing across all your relevant data at speed is critical to the success of your team’s ability to stop threats at scale. Elastic Security can help you drive holistic visibility for your security team, and operationalize that visibility to solve SIEM use cases, strengthen your threat hunting practice with machine learning and automated detection, and more.
Rethinking Ops
Looking back at my years working with infrastructure and going through it’s changes, I believe its time we start to rethink Operations because clearly this model of Ops as cluster or infrastructure admins does not scale. Developers will always out-demand their capacity to supply. Either your headcount is out of control or your ability to innovate and deliver is severely hamstrung. Operations becomes this interrupt-driven thing where we’re just fighting fires as they happen.
How We're Cutting $360K From Anodot's Annual Cloud Costs
With the pandemic forcing businesses worldwide to reboot, many have no choice but to exact drastic cost-cutting measures to keep the lights on. Cloud computing is an expense incurred by every digital business that, unlike many other operating costs, is largely variable.
Tracking Kubernetes Spend With CloudZero in 3 Easy Steps
If you are looking to account for your container costs and understand how your AWS Kubernetes or EKS cluster spend maps onto your workloads, this guide was made for you! In this post we will walk through the steps to get up and running with CloudZero and Amazon Container Insights fast. CloudZero has integrated with Amazon CloudWatch Container Insights for its strength as a secure and automated solution for sharing container metrics within AWS.
Data Security for Big Data
Big data security is a term used for all collective measures taken to protect both data and analytical processes from theft, attacks or all other malicious activities. Just like other forms of cybersecurity, big data security is about attacks originating from every online or offline sphere. Companies operating on the cloud face multiple challenges including online information theft, DDoS attacks and ransomware.
Top Three Takeaways From Our Multi-Cloud Connectivity Webinar
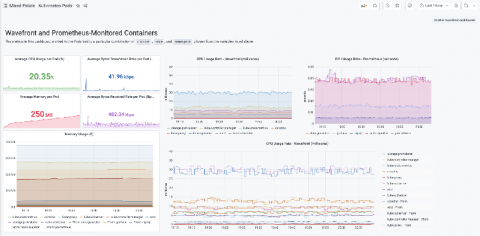
The new Wavefront Enterprise plugin brings the high-scale, high-speed SaaS to your Grafana dashboards
In early 2020, the Wavefront team was merged into the newly formed “Tanzu” portfolio under VMware’s Modern Applications business unit.
MLTK Smart Workflows
I’m excited to announce the launch of a new series of apps on Splunkbase: MLTK Smart Workflows. These apps are domain-specific workflows, built around specific use cases, that can be used to help you develop a set of machine learning models with your data. In this blog post, I’d like to take you through the process we adopted for developing the workflows.