Operations | Monitoring | ITSM | DevOps | Cloud
Free website monitoring-is it worth anything?
Today, we’ll take a look at the ubiquitous offers of free monitoring of the availability of websites. Why are they free, how do they differ from paid services and is it worth using them?
Whitelist Email Addresses: Thunderbird
TLDR; "If you expect to receive important emails from a trusted email address it is worth whitelisting the address to make sure that emails won't be accidentally blocked by an overzealous email client." In this post we show you how to do it in Mozilla Thunderbird by selecting the correct address book settings and adding the email address as a contact in your address book...
Meeting Compliance Regulations with SIEM and Logging
SIEM and log management provide security to your organization; these tools allow your security analysts to track events such as potential and successful breaches of your system and react accordingly. Usually, it doesn’t matter how you ensure your organizational safety-as long as you do.
A Quick Guide to Encrypted Messaging
With it now being so easy to share information, we have a tendency to over-divulge. We check into public places online, tell the world when we’re going on holiday and where, and send and receive risqué photos. However, when it became public knowledge that the NSA, internet service providers, and trusted social media platforms were able to monitor our private messages, the choice to share or not to share was taken away from us.
AWS monitoring 101: Metrics to watch out for
Amazon Web Services (AWS) is one of the most popular public cloud providers today. Over the years, AWS’ services have expanded from cloud computing to application development and security. To retain the reliability, availability, and performance of your AWS instances, an AWS cloud monitoring solution is a must. It’s critical for AWS monitoring tools to collect data from all parts of your AWS service, so that multi-point failure can be easily debugged.
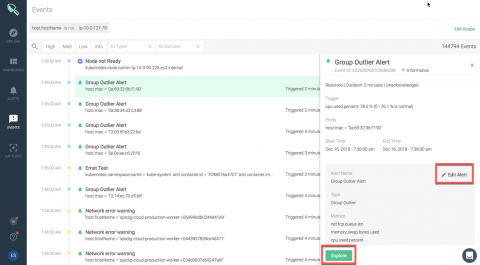
Unveiling Sysdig Monitor Events
At Sysdig, we have built a cloud-native intelligence platform to create a single, more effective way to monitor and secure your critical applications. We want to empower our users to quickly identify critical events and focus on events that need the most attention from you.
Jenkins Build Monitoring with the ELK Stack and Logz.io
Jenkins is an extremely popular, open-source, continuous integration tool used for running tests, building code, and subsequently pushing to staging and then production. In a previous post, I outlined instructions for collecting, analyzing and visualizing Jenkins system logs.
The Key to Keeping Stakeholders Informed during Incident Management
Keeping stakeholders informed and engaged during a service disruption is a critical part of incident management. Now with free stakeholder licenses from Opsgenie, all of the key people in your organization can view service status pages and receive communications for incidents that affect them.
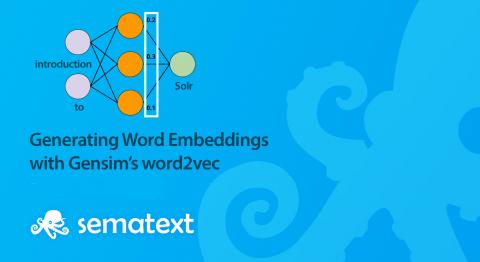
Generating Word Embeddings with Gensim's word2vec
During our Activate presentation, we talked about how to do query expansion by dynamically generating synonyms. Instead of statically defining synonyms lists, we showed a demo of how you could use word2vec to derive synonyms from a dataset. Before we start, check out a useful Solr Cheat Sheets to guide you through Solr and help boost your productivity and save time.