Understanding Microsoft's Latest Zero-Day Vulnerability #patch
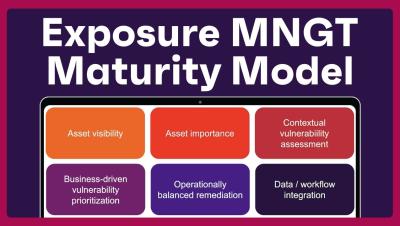
Microsoft has identified a zero-day vulnerability in the Windows kernel, rated 7.0 on the CVSS scale. Organizations often misprioritize vulnerabilities, focusing on high-severity scores instead of those actively exploited. Many lower-severity vulnerabilities are chained by attackers. A risk-based approach to vulnerability management is crucial. Current Windows OS versions are affected, and organizations should consider Extended Security Updates to mitigate risks as more zero days are anticipated.