Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on Log Management, Log Analytics and related technologies.
Botnet App for Splunk
It’s only taken me two years, but I’ve finally answered a question that I was asked by Derek King – “Can we use ML to detect botnets?” Thanks Derek, that was a pretty heavy question to be asked in your first week at Splunk, especially when you have no Splunk experience… You can judge the results here using the Botnet App for Splunk.
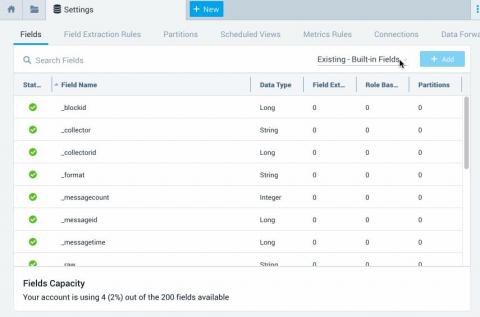
Analyze Metric and Event Data on the Same Platform
Analyze both metric and event data on the same platform regardless of source or structure. With Splunk metric indexes, you can quickly and easily ingest, store, and analyze metrics — whether in the Analytics Workspace or with SPL — so you can deliver positive business results. Get the most value out of your data with Splunk.
Elasticsearch Update Index Settings
You’ve created the perfect design for your indices and they are happily churning along. However, in the future, you may need to reconsider your initial design and update the Elasticsearch index settings. This might be to improve performance, change sharding settings, adjust for growth and manage ELK costs. Whatever the reason, Elasticsearch is flexible and allows you to change index settings. Let’s learn how to do that!
Tutorial: Logging with journald
If you’re using Linux, I’m sure you bumped into journald: it’s what most distros use by default for system logging. Most applications running as a service will also log to the journal. So how do you make use of these logs to: In this post, we’ll answer all the above and more. We will dive into the following topics: There are lots of other options to centralize journal entries, and lots of tools to help.
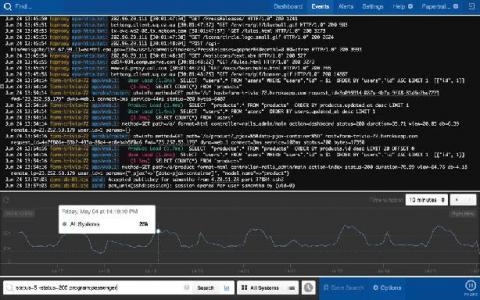
Google GSuite to Splunk HEC Configuration
Google Cloud recently expanded the list of GSuite audit logs that you can share with your Cloud Audit Logs, part of your organization’s Google Cloud’s account. This is awesome news and allows administrators to audit and visualize their GSuite Admin and Login activity in Splunk real-time via the same method used to stream Google Cloud logs and events into Splunk, using the Google-provided Pub/Sub to Splunk Dataflow template.
5 Reasons You Should Start Analyzing Your Logs
Sumo Logic Recognized as Data Analytics Solution of the Year Showcasing the Power of Continuous Intelligence
Protecting Your Assets: It's Not Just About Servers and Laptops!
In most of our blogs, we spend a TON of time going on about protecting our endpoints, looking at sysmon, checking the firewall, correlating IDS data and the like… Today, we're going to shift gears a bit and look at security from a different angle. Recently, there has been a tremendous focus on the shifting paradigm of a workforce that primarily resides in corporate offices, to a highly virtual workforce sitting at their kitchen tables.
The Pivotal Role of Log Analytics in Modern IT Infrastructures
In this survey of over 200 CIOs in the US, the IDC analyses the critical role played by Log Analytics in any modern infrastructure.