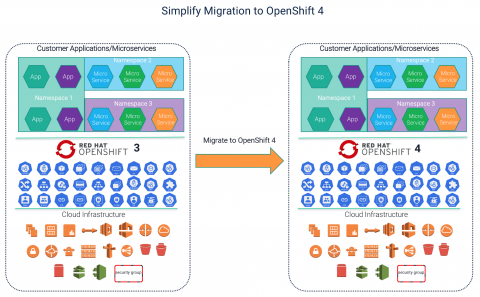
Simplify Migration from OpenShift 3 to 4
This is a guest post written by Appranix. Now that Red Hat OpenShift 4 has officially been released, it’s time to start thinking about migration from Red Hat OpenShift Container Platform 3 to OpenShift Container Platform 4. You can check out the details about the differences between OpenShift 3 and 4 here. One of the biggest differences between OpenShift 3 and 4 is how OpenShift 4 clusters operate using immutable and automated infrastructure enabled by RHEL CoreOS and automation.