Operations | Monitoring | ITSM | DevOps | Cloud
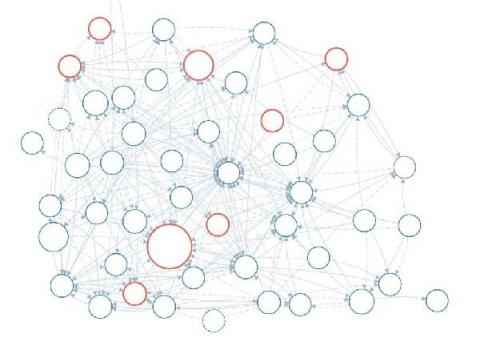
Service Map & Dashboards Provide Insight into Health and Dependencies of Microservice Architecture
Dependency Confusion Attacks
You must secure your software supply chain. Now, more than ever, it is vital. For a long time, a primary concern in security was malicious actors exploiting inherent weaknesses in software. Privilege escalations, SQL injections, race conditions etc. These are, of course, still a concern and should be afforded the attention that they deserve. But now, there is another worry, one that is arguably even more important – A Supply Chain Attack.
Your guide to SSL certificates as an online customer
We’re all familiar with the internet, especially since we use it to do almost all of our daily activities. Since the days of that familiar buzzing noise of AOL dial-up as it connected to somewhere out there in the stratosphere, we’ve been hooked on the internet and its vast space that holds endless amounts of information, ready for us to tap into right at our fingertips.
Centralized Log Management for Cloud Streamlines Root Cause Analysis
Cloud services make the daily tasks of business easier. They enable remote workforce collaboration, streamline administrative tasks, and reduce capital costs. However, these “pros” come with a few “cons.” The IT stack’s increased complexity means staff work across divergent log management tools when something breaks. Centralized log management for the cloud makes root cause analysis easier by aggregating all event log data in a single location.
10 Server Maintenance Tips for Efficient Server Maintenance
Just like your commercial vehicles or HVAC systems, servers require regular maintenance to ensure they are operating effectively and optimally. So, we decided to compile a list of server maintenance tips you should be doing. Keep in mind, these server maintenance tips are meant to be used as a guide to help you develop your server maintenance checklist and schedule.
Security operations center, Part 3: Finding your weakest link
Any organization with data assets is a possible target for an attacker. Hackers use various forms of advanced cyberattack techniques to obtain valuable company data; in fact, a study by the University of Maryland showed that a cyberattack takes place every 39 seconds, or 2,244 times a day on average. This number has increased exponentially since the COVID-19 pandemic forced most employees to work remotely, and drastically increased the attack surface of organizations around the world.
5 reasons integrated patch and vulnerability management mitigates risks swiftly and efficiently
ESG research on cyber risk management, which involved 340 cybersecurity professionals, revealed that 40 percent felt tracking patch and vulnerability management over time was their biggest challenge.
Migrating our Blog back to our website
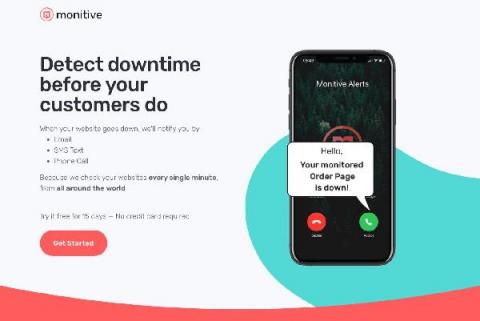
Two years ago I decided to migrate our Monitive blog to a Medium publication called Once Upon A Site. This happened for several reasons, including the fact that we are getting more readers on Medium than we were getting on our blog at the time. Of course, all while ignoring all there is to SEO. This was a good call at the time.
Script Writing: A Crash Course on User Journey Selectors
User Journeys are a powerful tool for ensuring key processes across your site are working correctly. They follow a scripted set of instructions to interact with your pages like a human visitor does – and to identify issues as they come up. We offer a “Managed Service” for looking after your User Journey scripts, or you might prefer to use our script builder to write your own.