Operations | Monitoring | ITSM | DevOps | Cloud
Extended BPF Keynote Overview - Ubuntu Masters
Scaling and Delivering Applications Keynote Overview - Ubuntu Masters
Migration Path to Linux Container Orchestration Keynote Sizzle - Ubuntu Masters
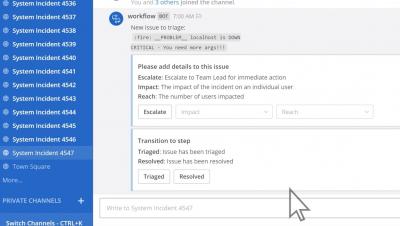
Mattermost Incident Response Workflows App - now in alpha
5 Reasons Why IT Asset Management Is Key to Your Business
The holiday season is always a good time to slow down, meditate, and be grateful for family, friends, and the blessings you have in your life. And believe it or not, I think this is a good practice to do in IT as well. You’re fighting the good fight day after day, extinguishing fires, battling resource and budget constraints, and dealing with more than enough on your Christmas dinner plate.
Alternative to Splunk: Pandora FMS as a monitoring tool
The American magazine “Fortune” specializes in global banking, business and finance… What does it have to do with monitoring? Well, in one of its annual lists, the Fortune 100 (the largest companies on the planet), 92 companies use Splunk software… If we compare by volume of money, yes, Splunk would be the best software and that’s where this article would end.
Automating the install of Elastic Cloud Enterprise on AWS with Ansible
So you want to install Elastic Cloud Enterprise (you know, the orchestration solution for the Elastic Stack that simplifies and standardizes how you deploy, upgrade, resize, configure, and monitor one to many clusters from a single UI/API) Installing ECE on one host isn’t tough. Installing it on two isn’t much harder. However, when you start dealing with 3, 5, 7, 11, etc., the complexity grows, as does the work involved in operating and maintaining (upgrading!) it all.
Storing and enriching alerts for information security with Elasticsearch
Within Elastic, the information security team is tasked with security detection and analytics, among many other activities of a typical information security team. To find abnormal and malicious behavior within our environment we leverage Elastic SIEM for investigations and threat hunting. When we find a pattern of behavior we want to be alerted on during an investigation or hunt we take the request JSON behind our investigation and put in to Watcher for alerting.
AIOps and Smart Alerting
Smart Alerting is not enough. Effective deployment of AIOps requires an independent platform capable of interacting with all technologies along the path from signal to response.