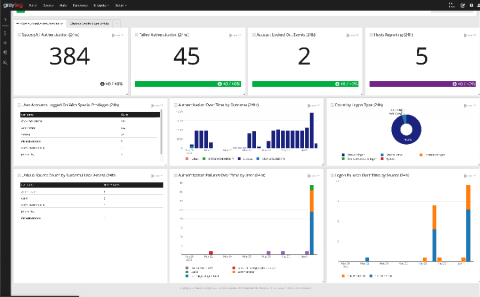
Announcing Graylog Illuminate for Authentication
Graylog Illuminate for authentication is a brand new offering designed by our Enterprise Intelligence team. It eliminates the manual setup necessary to detect, monitor, and analyze authentication activities and issues across your IT infrastructure by providing pre-built Dashboards, Alerts, and data enrichment. Initially, Graylog Illuminate for Authentication will address Windows authentication issues and activities. We will release additional data sources in the coming weeks so stay tuned!