Operations | Monitoring | ITSM | DevOps | Cloud
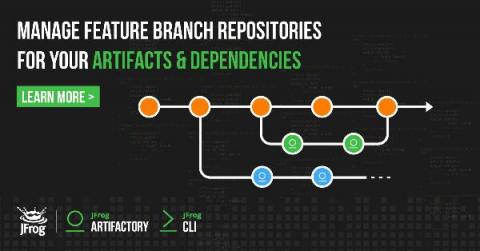
Automating your Feature Branch Repository Management with JFrog CLI
Ivanti Neurons for Healing: Shift All the Way Left to Self-Healing
If you are an IT professional, you are technical. You love technology. You love to dabble. You enjoy the thrill that comes from troubleshooting problems and finding a solution. But you probably don’t want to troubleshoot and fix problems all day. There are other interesting things to do. IT can be strategic in helping companies improve their top and bottom line. The complexity of IT continues to increase. The good news is that the need for talented IT staff also continues to grow.
What should a CIO or CTO know about IoT?
If you occupy positions of certain responsibility (such as CIO or CTO) and you do not know what is necessary about IoT, you run the risk of being out of the game. So here in this article is what you need to know about IoT. The following post is not intended to be a full encyclopedia on the Internet of Things.
Protect your Elasticsearch deployments against attacks like "meow bot" - for free
The issue of unsecured databases is growing. In 2019, 17 percent of all data breaches were caused by human error — twice as many as just a year before. And the IBM/Ponemon 2019 report found that the estimated probability of a company having repeated data breaches within two years grew by 31 percent between 2014 and 2019. Why is this happening?
Hybrid Cloud: How to Build an Effective Strategy
Cloud computing is a foundational platform for modern businesses, enabling digital transformation and supporting organizational agility. The benefits of putting applications in the cloud are well documented: flexibility, scalability, and reliability with a lower capex investment.
Gremlin
Part 2: How to Build Monitoring Dashboards that are Grafana-Compatible with Logz io
Cyber Security: Understanding the 5 Phases of Intrusion
Here at Graylog, we have recently had an increase in conversations with security teams from leading companies. We want to share our key findings with the Graylog community. The good thing is that cybercriminals use a methodical approach when planning an attack. By understanding their process and knowing your network, you will be better prepared and able to stay one step ahead.