Operations | Monitoring | ITSM | DevOps | Cloud
Using Network Visibility to Grow Your MSP Business
Get Network Device Warranty & Software Status Automatically with Auvik & Cisco
Benchmarking the Digital Workplace
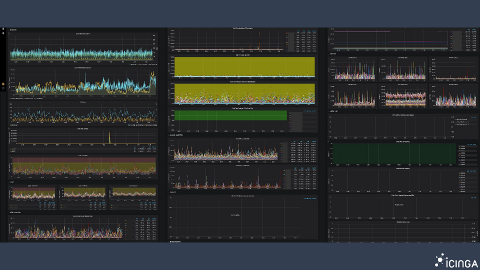
How Not to Fail at Visualization
As a longtime systems engineer, Blerim Sheqa knows all about using tools like Grafana to debug issues in infrastructures. Currently the CPO of Icinga, an open source monitoring software, he gave a talk at GrafanaCon LA about how not to fail at visualization.
Prometheus and Docker: Monitoring Your Environment
Coming back from Monitorama, I had a chance to sit back and start playing with some tools to see how they worked. Prometheus is a pretty ubiquitous tool in the monitoring space, it's pretty easy to spin up, and is open-source. Having a very active community of engaged developers means finding help articles or guides is easy. We are also going to use Grafana to build nicer looking graphs based on API queries from Prometheus.
SaneBox: Using Artificial Intelligence for Smarter Email Services
We all struggle with overloaded emails and are always on the lookout for methods to ease this burden. To make a clutter-free inbox a reality, help comes in the form of Sanebox. This is a software program made especially to clean up and effectively organize the client’s inbox. This simple software program works by taking a complete overview of your email.
Why the LogDNA Agent Runs As Root
One question that customers often ask is “why does the LogDNA agent need to run as root?” With IT departments and DevSecOps teams pushing to secure systems against cyberattacks, running a cloud-based logging agent as root sounds like a huge risk. While it’s true that you should avoid running applications as root, there are several reasons why our agent runs as root out of the box and several ways that we reduce your risk of attack.
Write to S3 and call other Lambdas with Python
Many people writing about AWS Lambda view Node as the code-default. I’ve been guilty of this in my own articles, but it’s important to remember that Python is a ‘first-class citizen’ within AWS and is a great option for writing readable Lambda code. Take a look at these two starter examples of writing functionality in Python.