Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on Log Management, Log Analytics and related technologies.
Get the HEC Out of Splunk App for Infrastructure
The Splunk App for Infrastructure (SAI) has changed the game when it comes to IT Operations monitoring and alerting of metrics and logs. The App provides a uniform and dynamic overview dashboard, and an analysis workspace for a simple method to work with metrics.
DevOps Best Practices for CI CD and Observability
Mitigate Logging Costs While Maintaining Full Observability with Logz.io
Considering the scale of log data that modern cloud environments generate, it’s oftentimes prohibitively expensive to index all of it. For monitoring and logging, cost management is just as important as in other parts of the business. Whether sudden spikes of log data overwhelm databases or good business generates more activity in your environment, teams should anticipate and mitigate the steep costs that result from high log volumes.
How to implement Prometheus long-term storage using Elasticsearch
Prometheus plays a significant role in the observability area. An increasing number of applications use Prometheus exporters to expose performance and monitoring data, which is later scraped by a Prometheus server. However, when it comes to storage, Prometheus faces some limitations in its scalability and durability since its local storage is limited by single nodes.
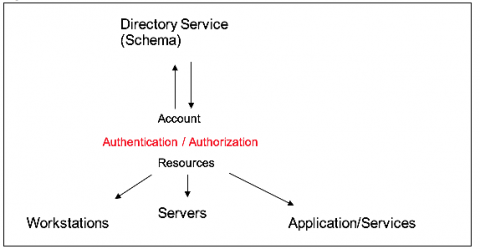
Profiling "VIP Accounts" Part 1
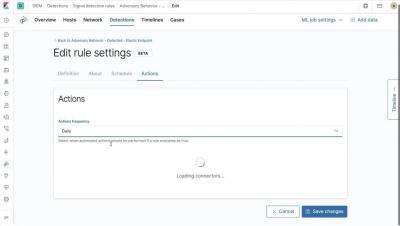
Elastic Stack 7.7.0 released
We are pleased to announce the general availability of version 7.7 of the Elastic Stack. Like most Elastic Stack releases, 7.7 packs quite a punch. But more than the new features, we’re most proud of the team that delivered it. A feature-packed release like this is special during normal times. But it’s extra special today given the uncertain times we are in right now.
Best Practices for Logging in AWS Lambda
Visualizing the Global Evolution of COVID-19 With VR
Over the past few weeks, Splunk has created a number of different tools to help bring data to the COVID-19 crisis. These tools, such as a public dashboard, an app on Github, and a Mobile Dashboard can be used to identify locations of outbreaks, find correlations and more.