Operations | Monitoring | ITSM | DevOps | Cloud
Catchpoint and Webpagetest.org join forces
WebPageTest is the industries most popular and widely used open-source web performance testing platform.
Leveraging behavior analytics and machine learning algorithms in your PAM strategy
Modern technologies like machine learning (ML) algorithms can introduce a forward-thinking outlook to privileged access management (PAM) and enable enterprises to predict emerging access risks in real time. ML-based anomaly detection systems can deeply analyze raw data collected around privileged activity, profile standard user behavior patterns, and then surveil future operations to detect any deviations from the norm, such as server logins after office hours.
ChartCenter Walkthrough with Rookout
Do you know how to use a chart repository for hosting and sharing Helm Charts? In this video, Rookout's walks us through JFrog’s ChartCenter, and shows us how to add a repository. ChartCenter is a free chart repository which makes it easy for the development community to upload and share charts with other developers.
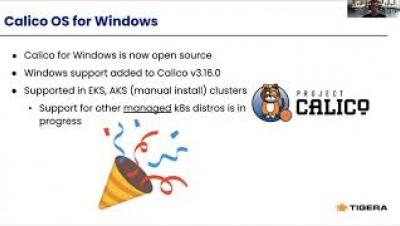
How to Secure Mixed Linux/Windows Clusters with Calico Policy
Calico is the only cross-platform CNI and Network Policy engine available today and is currently powers more than 150,000 known clusters across millions of nodes worldwide. Many organizations have .NET and windows workloads that they are or will eventually modernize and deploy to Kubernetes. We have been collaborating with Microsoft and joint customers over the past few years to bring Calico to the Windows platform.
Microk8s and Charmed ceph at the edge
Learn how to get compact and resilient Kubernetes in under 10 minutes.
How To Succeed When Adopting A Multi Cloud Environment
Today, a vast majority of companies are working with multiple cloud providers. But moving IT operations to the cloud has significant consequences they need to deal with. Discover how Broadcom helps customers to manage critical workloads in multi-cloud environments, simplifying and accelerating the deployment of new business services.
How Automation Helps The Site Reliability Engineer
Automation has been with us for decades now and with years of experience and experimentation we are arriving at a best practice known as site reliability engineering. Site reliability engineering seeks to manage the risk imposed from multiple agile changes to protect business revenues and sustain positive customer experiences.
How to install pandora fms in centOS8?
Discover in this tutorial how to install Linux agents in Pandora FMS.