Operations | Monitoring | ITSM | DevOps | Cloud
Developing a Dedicated Log Collection & Management Plan
When it comes to your network and server processes, one of the key ways your IT team will collect data and insight is through event logging. Collecting the right event data will help inform both essential processes and services, as well as your network security measures, which is why having the proper collection plan in place is key. At Pandora FMS, we offer a host of comprehensive log collection and network monitoring solutions designed to be easily customized.
The Ultimate Guide to AWS DynamoDB
DynamoDB is a key-value and document database with single-digit millisecond response times at any scale. It’s a fully managed durable database with built-in security, backup and restore capabilities. A keyword you’ll often hear with DynamoDB is that it is a NoSQL database, which simply means it doesn’t use the traditional SQL query language used in relational databases.
How Long Should You Hang Onto Your Data?
One of the most common questions that businesses operating under GDPR, LGPD or other similar data regulations have is how long should you keep data? As answers to this question typically seem to vary widely to clear up confusion, we’ve gathered insights from business leaders & specialists across a variety of industries to try and answer this question and shed light on what are reasonable timeframes to keep hold of data, whether that may be financial, employee or other potentially sensitive data.
Support via Emoji
Emojis are finally useful for more than sentiment or sass. Cloudsmith Engineering can now be raised in emergency situations via a single emoji - SOS. And it’s been used for the first, and so far only, time. At Cloudsmith, we pride ourselves on our reactive (and in many cases proactive) support. We architected and built the platform with monitoring in mind allowing us to provide transparency of internal operations to you and us.
3 Ways to Send Emails with Ruby
For many developers, Ruby on Rails framework not only allows them to build web applications, websites, and efficient database solutions, but it can help them optimize mailing operations. You can easily use Ruby on Rails mailer, an automatic tool to build transactional messages of any kind, and make proper authentication. In this article, we review three main ways to work with email sending in RoR, which include some Ruby gems, the Net::SMTP class, and the facilities of the Socket system.
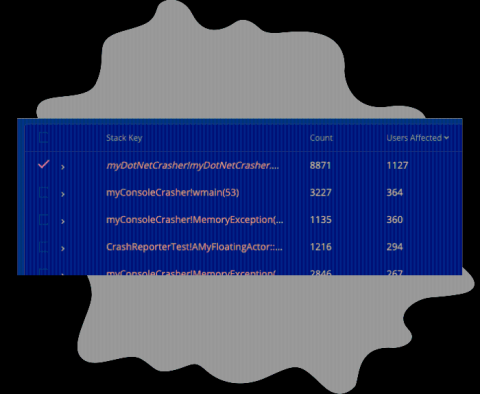
New Feature: Number of Users Affected by a Crash
We've just released a way to track the number of users affected by a crash! If you navigate to the Summary page, you'll now see a column labeled 'Users Affected’, this column shows how many unique users have been affected for each row in the crash summary table. With the data provided by this new column, you’ll have additional information available for prioritizing fixes. The ‘Count’ column is unchanged, and reports the total number of crashes reported by all users.
Your Top 3 AIOps Questions Answered
Artificial intelligence for IT Operations (AIOps) still sounds like something from the future to a lot of IT professionals. Maybe you’ve heard about the benefits but don’t think your organization is ready. In these three short, informative videos, Kia Behnia, Vice President of IT Operations, addresses three key questions IT pros still have when it comes to AIOps.
Build a resilient cybersecurity framework by transforming your IT team into a security team
More organizations than ever before have shifted to a hybrid work culture to reduce the impact of COVID-19. This unprecedented change has not only given rise to new security challenges, but has also considerably increased the surface area available for an attack. A blend of personal and corporate endpoints in use, geographical spread of resources, and a sharp spike in the overall number of security threats have further complicated the already labor-intensive security landscape.
Five worthy reads: Every month should be Cybersecurity Awareness Month!
Five worthy reads is a regular column on five noteworthy items we’ve discovered while researching trending and timeless topics. Organizations on a global scale observe Cybersecurity Awareness Month to educate and instruct their employees on cybersecurity best practices. This week we highlight some cybersecurity trends that are shaping the industry today.